| Revision as of 05:49, 24 October 2014 view sourceWidr (talk | contribs)Edit filter managers, Autopatrolled, Administrators303,507 editsm Reverted 1 edit by Shahnawaz hussain nagori using STiki← Previous edit | Latest revision as of 00:21, 24 November 2024 view source GoingBatty (talk | contribs)Autopatrolled, Extended confirmed users, IP block exemptions, Pending changes reviewers, Rollbackers640,466 edits bad link repair, replaced: Supreme Court → Supreme CourtTag: AWB | ||
| Line 1: | Line 1: | ||
| {{Short description|Instructions a computer can execute}} | |||
| @Shahnawaz Hussain Nagori | |||
| {{Other uses}} | {{Other uses}} | ||
| {{pp|small=yes}} | |||
| {{Refimprove|date = September 2013}} | |||
| {{Use dmy dates|date=May 2017}} | |||
| ] language]] | |||
| '''Software''' consists of ]s that instruct the ] of a ].<ref name="pis-p16">{{cite book | |||
| | last = Stair | |||
| | first = Ralph M. | |||
| | title = Principles of Information Systems, Sixth Edition | |||
| | publisher = Thomson | |||
| | year = 2003 | |||
| | page = 16 | |||
| | isbn = 0-619-06489-7 | |||
| | quote = Software consists of computer programs that govern the operation of the computer. | |||
| }}</ref> Software also includes design documents and specifications. | |||
| The history of software is closely tied to the development of digital computers in the mid-20th century. Early programs were written in the ] specific to the hardware. The introduction of ]s in 1958 allowed for more human-readable instructions, making ] easier and more portable across different ]s. Software in a programming language is run through a ] or ] to ] on the architecture's hardware. Over time, software has become complex, owing to developments in ], ], and ]. | |||
| '''Computer software''', or simply '''software''' is any set of machine-readable instructions that directs a ]'s processor to perform specific operations. Computer software contrasts with ], which is the physical component of computers. Computer hardware and software require each other and neither can be realistically used without the other. | |||
| Software can generally be categorized into two main types: | |||
| Computer software includes ]s, ] and their associated documentation. The word software is also sometimes used in a more narrow sense, meaning ] only. Software is stored in ] and cannot be touched i.e. it is intangible.<ref>{{cite web | |||
| # ]s, which manage hardware resources and provide services for applications | |||
| | title = 'Software' from Collins Concise English Dictionary | |||
| # ], which performs specific tasks for users | |||
| | website = Wordreference.com | |||
| | publisher = Princeton University | |||
| | location = ] | |||
| | url = http://www.wordreference.com/definition/software | |||
| | accessdate = 2007-08-19 }}</ref> | |||
| The rise of ] has introduced the new software delivery model ] (SaaS). In SaaS, applications are hosted by a ] and ] over the ]. | |||
| At the lowest level, executable code consists of machine language instructions specific to an individual ] – typically a ] (CPU). A ] consists of groups of binary values signifying processor instructions that change the state of the computer from its preceding state. For example, an instruction may change the value stored in a particular storage location inside the computer – an effect that is not directly observable to the user. An instruction may also (indirectly) cause something to appear on a display of the computer system – a state change which should be visible to the user. The processor carries out the instructions in the order they are provided, unless it is instructed to "jump" to a different instruction, or interrupted. | |||
| The process of developing software involves several stages. The stages include ], ], ], ], and ]. ] and ] are critical aspects of software development, as ] and ] can lead to system failures and security breaches. Additionally, legal issues such as software licenses and intellectual property rights play a significant role in the distribution of software products. | |||
| Software written in a machine language is known as "machine code". However, in practice, software is usually written in ]s that are easier and more efficient for humans to use (closer to ]) than machine language.<ref>{{cite web|title=Compiler construction|url=http://www.cs.uu.nl/education/vak.php?vak=INFOMCCO}}</ref> High-level languages are translated, using ] or ] or a combination of the two, into machine language. Software may also be written in a low-level ], essentially, a vaguely ] representation of a machine language using a natural language alphabet. Assembly language is translated into machine code using an ]. | |||
| == |
==History== | ||
| {{ |
{{Main|History of software}} | ||
| ] is an essential invention to produce modern software systems.{{sfn|Jones|2014|pp=19, 22}}]] | |||
| The first use of the word ''software'' is credited to mathematician ] in 1958.{{sfn|Tracy|2021|p=2}} | |||
| The first programmable computers, which appeared at the end of the 1940s,{{sfn|Gabbrielli|Martini|2023|p=519}} were programmed in ]. Machine language is difficult to debug and not ] across different computers.{{sfn|Gabbrielli|Martini|2023|pp=520–521}} Initially, hardware resources were more expensive than ].{{sfn|Gabbrielli|Martini|2023|p=522}} As programs became complex, ] became the bottleneck. The introduction of ]s in 1958 ] the details of the hardware and expressed the underlying ]s into the code .{{sfn|Gabbrielli|Martini|2023|p=521}}{{sfn|Tracy|2021|p=1}} Early languages include ], ], and ].{{sfn|Tracy|2021|p=1}} | |||
| == |
==Types== | ||
| {{ |
{{See also|Software categories}} | ||
| <imagemap>File:Operating system placement.svg|thumb|A diagram showing how the ] software and ] are layered on a typical ]. The arrows indicate information flow. | |||
| rect 1 1 250 90 ] | |||
| rect 1 91 250 180 ] | |||
| rect 1 181 250 270 ] | |||
| rect 1 271 250 360 ] | |||
| </imagemap> | |||
| On virtually all computer platforms, software can be grouped into a few broad categories. | |||
| ] interacts with ] on a typical ]. The application software layer interfaces with the ], which in turn communicates with the ]. The arrows indicate information flow.]] | |||
| === Purpose, or domain of use === | |||
| There are two main types of software: | |||
| * ]s are "the ] that manages a computer's resources for its users and their ]s".{{sfn|Anderson|Dahlin|2014|p=6}} There are three main purposes that an operating system fulfills:{{sfn|Anderson|Dahlin|2014|p=7}} | |||
| * ''']''', which uses the computer system to perform special functions or provide ] beyond the basic operation of the computer itself. There are many different types of application software, because the range of tasks that can be performed with a modern computer is so large - see ]. | |||
| **Allocating resources between different applications, deciding when they will receive ] (CPU) time or space in ].{{sfn|Anderson|Dahlin|2014|p=7}} | |||
| * ''']''', which is designed to directly operate the ], to provide basic functionality needed by users and other software, and to provide a platform for running application software.<ref>{{cite web|title=System Software|url=http://home.olemiss.edu/~misbook/sfsysfm.htm|publisher=The University of Mississippi}}</ref> System software includes: | |||
| **Providing an interface that abstracts the details of accessing ] details (like physical memory) to make things easier for programmers.{{sfn|Anderson|Dahlin|2014|p=7}}{{sfn|Tanenbaum|Bos|2023|p=5}} | |||
| ** ]s, which are essential collections of software that manage resources and provides common services for other software that runs "on top" of them. ]s, ]s, ] and ]s are core parts of operating systems. In practice, an operating system comes bundled with additional software (including application software) so that a user can potentially do some work with a computer that only has an operating system. | |||
| **Offering common services, such as an interface for accessing network and disk devices. This enables an application to be run on different hardware without needing to be rewritten.{{sfn|Anderson|Dahlin|2014|pp=7, 9, 13}} | |||
| ** ]s, which operate or control a particular type of device that is attached to a computer. Each device needs at least one corresponding device driver; because a computer typically has at minimum at least one input device and at least one output device, a computer typically needs more than one device driver. | |||
| * ] runs on top of the operating system and uses the computer's resources to perform a task.{{sfn|Anderson|Dahlin|2014|pp=6-7}} There are many different types of application software because the range of tasks that can be performed with modern computers is so large.{{sfn|Jones|2014|p=121}} Applications account for most software{{sfn|Tracy|2021|p=66}} and require the ] provided by an operating system, and often other applications, in order to function.{{sfn|Tracy|2021|p=72}} | |||
| ** ], which are computer programs designed to assist users in maintenance and care of their computers. | |||
| * ''']''' or ''']''', which are computer programs developed to harm and disrupt computers. As such, malware is undesirable. Malware is closely associated with computer-related crimes, though some malicious programs may have been designed as ]s. | |||
| ] (IaaS), ] (PaaS), and ] (SaaS)|upright=2.4|center]] | |||
| === Nature, or domain of execution === | |||
| Software can also be categorized by how it is ]. Traditional applications are purchased with a perpetual ] for a specific version of the software, downloaded, and run on hardware belonging to the purchaser.{{sfn|O'Regan|2022|p=386}} The rise of ] and ] enabled a new model, ] (SaaS),{{sfn|Campbell-Kelly|Garcia-Swartz|2015|pp=156-157}} in which the provider hosts the software (usually built on top of rented ] or ]s){{sfn|Rosati |Lynn|2020|p=23}} and provides the use of the software to customers, often in exchange for a ].{{sfn|O'Regan|2022|p=386}} By 2023, SaaS products—which are usually delivered via a ]—had become the primary method that companies deliver applications.{{sfn|Watt|2023|p=4}} | |||
| * ] such as ]s and ], as well as ] and ] applications (called "]"). (There is a push in some parts of the software industry to merge desktop applications with mobile apps, to some extent. ], and later ], tried to allow the same style of application user interface to be used on desktops and laptops, mobile devices, and hybrid tablets.) | |||
| * ] scripts are pieces of software traditionally embedded in ] that are run directly inside the ] when a web page is loaded without the need for a web browser plugin. Software written in other programming languages can also be run within the web browser if the software is either translated into JavaScript, or if a web browser plugin that supports that language is installed; the most common example of the latter is ] scripts, which are supported by the ] plugin. | |||
| * ], including: | |||
| ** ], which usually run on the ] and output dynamically generated web pages to web browsers, using e.g. ], ] or ], or even ]. In modern times these commonly include some JavaScript to be run in the web browser as well, in which case they typically run partly on the server, partly in the web browser. | |||
| * ] and extensions are software that extends or modifies the functionality of another piece of software, and require that software be used in order to function; | |||
| * ] resides as firmware within ], devices dedicated to a single use or a few uses such as ] and ] (although some embedded devices such as wireless chipsets can ''themselves'' be part of an ordinary, non-embedded computer system such as a PC or ]).<ref>{{cite web|title=Embedded Software—Technologies and Trends|url=http://www.computer.org/csdl/mags/so/2009/03/mso2009030014.html|publisher=IEEE Computer Society|accessdate=May–June 2009}}</ref> In the embedded system context there is sometimes no clear distinction between the system software and the application software. However, some embedded systems run ], and these systems do retain the distinction between system software and application software (although typically there will only be one, fixed, application which is always ran). | |||
| * ] is a special, relatively obscure type of embedded software which tells the processor ''itself'' how to execute machine code, so it is actually a lower level than machine code.<ref>{{cite web|title=Microcode|url=http://www.princeton.edu/~achaney/tmve/wiki100k/docs/Microcode.html|publisher=Princeton University}}</ref> It is typically proprietary to the processor manufacturer, and any necessary correctional microcode software updates are supplied by them to users (which is much cheaper than shipping replacement processor hardware). Thus an ordinary programmer would not expect to ever have to deal with it. | |||
| ==Software development and maintenance== | |||
| === Programming tools === | |||
| ] from 1988. The numbers represent the typical cost of each phase.]] | |||
| {{Main|Programming tool}} | |||
| Software companies aim to deliver a high-quality product on time and under budget. A challenge is that ] is often inaccurate.{{sfn|O'Regan|2022|p=7}} ] begins by conceiving the project, evaluating its feasibility, analyzing the business requirements, and making a ].{{sfn|O'Regan|2022|p=5}}{{sfn|Dooley|2017|p=1}} Most software projects speed up their development by ] or incorporating existing software, either in the form of ] (COTS) or ].{{sfn|O'Regan|2022|pp=18, 110-111}}{{sfn|Tracy|2021|pp=43, 76}} ] is typically a combination of manual ] by other engineers{{sfn|O'Regan|2022|pp=117-118}} and automated ]. Due to time constraints, testing cannot cover all aspects of the software's intended functionality, so developers often focus on the most critical functionality.{{sfn|O'Regan|2022|p=54}} ]s are used in some safety-critical systems to prove the correctness of code,{{sfn|O'Regan|2022|p=267}} while ] helps to ensure that the product meets customer expectations.{{sfn|O'Regan|2022|p=20}} There are a variety of ], which vary from completing all steps in order to concurrent and iterative models.{{sfn|O'Regan|2022|p=9}} Software development is driven by ] taken from prospective users, as opposed to maintenance, which is driven by events such as a change request.{{sfn|Tripathy |Naik|2014|p=26}} | |||
| Programming tools are also software in the form of programs or applications that ] (also known as ''programmers, coders, hackers'' or ''software engineers'') use to create, ], ] (i.e. improve or fix), or otherwise ] software. Software is written in one or more programming languages; there are many programming languages in existence, and each has at least one implementation, each of which consists of its own set of programming tools. These tools may be relatively self-contained programs such as ]s, ]s, ], ], and ]s, that can be combined together to accomplish a task; or they may form an ] (IDE), which combines much or all of the functionality of such self-contained tools. IDEs may do this by either invoking the relevant individual tools or by re-implementing their functionality in a new way. An IDE can make it easier to do specific tasks, such as searching in files in a particular project. Many programming language implementations provide the option of using both individual tools or an IDE. | |||
| Frequently, software is ] in an incomplete state when the development team runs out of time or funding.{{sfn |Reifer|2012|p=22}} Despite ] and ], virtually all software contains ] where the system does not work as intended. Post-release ] is necessary to remediate these bugs when they are found and keep the software working as the environment changes over time.{{sfn|Tripathy |Naik|2014|pp=4, 27}} New features are often added after the release. Over time, the level of maintenance becomes increasingly restricted before being cut off entirely when the product is withdrawn from the market.{{sfn|Tripathy |Naik|2014|p=89}} As software ], it becomes known as ] and can remain in use for decades, even if there is no one left who knows how to fix it.{{sfn|Tracy|2021|p=3}} Over the lifetime of the product, software maintenance is estimated to comprise 75 percent or more of the total development cost.{{sfn|Varga|2018|p=6}}{{sfn|Ulziit ''et al.''|2015|p=764}} | |||
| == Software topics == | |||
| Completing a software project involves various forms of expertise, not just in ]s but also testing, documentation writing, ], ], ], user support, ], and fundraising.{{sfn|Tucker |Morelli |de Silva |2011|p=7}}{{sfn|Stull|2018|pp=24-25}}{{sfn|Dooley|2017|p=1}} | |||
| === Architecture === | |||
| {{See also|Software architecture}} | |||
| Users often see things differently from programmers. People who use modern general purpose computers (as opposed to ]s, ]s and ]s) usually see three layers of software performing a variety of tasks: platform, application, and user software. | |||
| * Platform software: ] includes the ], ]s, an ], and typically a ] which, in total, allow a user to interact with the computer and its ]s (associated equipment). Platform software often comes bundled with the computer. On a ] one will usually have the ability to change the platform software. | |||
| * Application software: ] or Applications are what most people think of when they think of software. Typical examples include office suites and video games. ] is often purchased separately from computer hardware. Sometimes applications are bundled with the computer, but that does not change the fact that they run as independent applications. Applications are usually independent programs from the operating system, though they are often tailored for specific platforms. Most users think of compilers, databases, and other "system software" as applications. | |||
| * User-written software: ] tailors systems to meet users' specific needs. User software include spreadsheet templates and ] templates. Even email filters are a kind of user software. Users create this software themselves and often overlook how important it is. Depending on how competently the user-written software has been integrated into default application packages, many users may not be aware of the distinction between the original packages, and what has been added by co-workers. | |||
| ==Quality and security== | |||
| === Execution === | |||
| {{main article|Software quality|Computer security}} | |||
| {{main|Execution (computing)}} | |||
| ] is defined as meeting the stated requirements as well as customer expectations.{{sfn|Galin|2018|p=3}} Quality is an overarching term that can refer to a code's correct and efficient behavior, its reusability and ], or the ease of modification.{{sfn|Galin|2018|p=26}} It is usually more cost-effective to build quality into the product from the beginning rather than try to add it later in the development process.{{sfn|O'Regan|2022|pp=68, 117}} Higher quality code will reduce lifetime cost to both suppliers and customers as it is more reliable and ].{{sfn|O'Regan|2022|pp=3, 268}}{{sfn|Varga|2018|p=12}} Software failures in ]s can be very serious including death.{{sfn|O'Regan|2022|pp=3, 268}} By some estimates, the cost of poor quality software can be as high as 20 to 40 percent of sales.{{sfn|O'Regan|2022|p=119}} Despite developers' goal of delivering a product that works entirely as intended, virtually all software contains bugs.{{sfn|Ablon|Bogart|2017|p=1}} | |||
| The rise of the Internet also greatly increased the need for ] as it enabled malicious actors to conduct ]s remotely.{{sfn|Campbell-Kelly|Garcia-Swartz|2015|p=164}}{{sfn|O'Regan|2022|p=266}} If a bug creates a security risk, it is called a ].{{sfn|Ablon|Bogart|2017|p=2}}{{sfn|Daswani |Elbayadi|2021|p=25}} ]es are often released to fix identified vulnerabilities, but those that remain unknown (]s) as well as those that have not been patched are still liable for exploitation.{{sfn|Daswani |Elbayadi|2021|pp=26-27}} Vulnerabilities vary in their ability to be ]ed by malicious actors,{{sfn|Ablon|Bogart|2017|p=2}} and the actual risk is dependent on the nature of the vulnerability as well as the value of the surrounding system.{{sfn|Haber |Hibbert|2018|pp=5-6}} Although some vulnerabilities can only be used for ] attacks that compromise a system's availability, others allow the attacker to ] and run their own code (called ]), without the user being aware of it.{{sfn|Ablon|Bogart|2017|p=2}} To thwart cyberattacks, all software in the system must be designed to withstand and recover from external attack.{{sfn|O'Regan|2022|p=266}} Despite efforts to ensure security, a significant fraction of computers are infected with malware.{{sfn|Kitchin |Dodge|2011|p=37}} | |||
| Computer software has to be "loaded" into the ] (such as the ] or ]). Once the software has loaded, the computer is able to ''execute'' the software. This involves passing ] from the ], through the system software, to the hardware which ultimately receives the instruction as ]. Each instruction causes the computer to carry out an operation – moving ], carrying out a ], or altering the ] of instructions. | |||
| ==Encoding and execution== | |||
| Data movement is typically from one place in memory to another. Sometimes it involves moving data between memory and registers which enable high-speed data access in the CPU. Moving data, especially large amounts of it, can be costly. So, this is sometimes avoided by using "pointers" to data instead. Computations include simple operations such as incrementing the value of a variable data element. More complex computations may involve many operations and data elements together. | |||
| <!-- This section is simply to long for this article and needs to be compressed into the intro above, or moved to the article itself .... | |||
| Instructions may be performed sequentially, conditionally, or iteratively. Sequential instructions are those operations that are performed one after another. Conditional instructions are performed such that different sets of instructions execute depending on the value(s) of some data. In some languages this is known as an "if" statement. Iterative instructions are performed repetitively and may depend on some data value. This is sometimes called a "loop." Often, one instruction may "call" another set of instructions that are defined in some other program or ]. When more than one computer processor is used, instructions may be executed simultaneously. | |||
| ===Programming languages=== | |||
| A simple example of the way software operates is what happens when a user selects an entry such as "Copy" from a menu. In this case, a conditional instruction is executed to copy text from data in a 'document' area residing in memory, perhaps to an intermediate storage area known as a 'clipboard' data area. If a different menu entry such as "Paste" is chosen, the software may execute the instructions to copy the text from the clipboard data area to a specific location in the same or another document in memory. | |||
| {{main|Programming language}} | |||
| ] for a computer program in ]. The gray lines are ] that explain the program to humans. When ] and ], it will give the output "]".]] | |||
| Programming languages are the format in which software is written. Since the 1950s, thousands of different programming languages have been invented; some have been in use for decades, while others have fallen into disuse.{{sfn|Tracy|2021|p=117}} Some definitions classify ]—the exact instructions directly implemented by the hardware—and ]—a more human-readable alternative to machine code whose statements can be translated one-to-one into machine code—as programming languages.{{sfn|Tracy|2021|pp=118–120}} Programs written in the ] used to create software share a few main characteristics: knowledge of machine code is not necessary to write them, they can be ] to other computer systems, and they are more concise and human-readable than machine code.{{sfn|Tracy|2021|pp=118–119}} They must be both human-readable and capable of being translated into unambiguous instructions for computer hardware.{{sfn|Kitchin |Dodge|2011|p=26}} | |||
| ===Compilation, interpretation, and execution=== | |||
| Depending on the application, even the example above could become complicated. The field of software engineering endeavors to manage the complexity of how software operates. This is especially true for software that operates in the context of a large or powerful ]. | |||
| <!-- ] --> | |||
| The invention of high-level programming languages was simultaneous with the ]s needed to translate them automatically into machine code.{{sfn|Tracy|2021|p=121}} Most programs do not contain all the resources needed to run them and rely on external ]. Part of the compiler's function is to link these files in such a way that the program can be executed by the hardware. Once compiled, the program can be saved as an ] and the ] (part of the operating system) can take this saved file and ] it as a ] on the computer hardware.{{sfn|Tracy|2021|pp=122-123}} Some programming languages use an ] instead of a compiler. An interpreter converts the program into machine code at ], which makes them 10 to 100 times slower than compiled programming languages.{{sfn|O'Regan|2022|p=375}}{{sfn|Sebesta|2012|p=28}} | |||
| ==Legal issues== | |||
| Currently, almost the only limitations on the use of computer software in applications is the ingenuity of the designer/programmer. Consequently, large areas of activities (such as playing grand master level chess) formerly assumed to be incapable of software simulation are now routinely programmed. The only area that has so far proved reasonably secure from software simulation is the realm of human art— especially, pleasing music and literature.{{Citation needed|date=June 2007}} | |||
| ===Liability=== | |||
| {{main article|Software product liability}} | |||
| Software is often released with the knowledge that it is incomplete or contains bugs. Purchasers knowingly buy it in this state, which has led to a legal regime where ] for software products is significantly curtailed compared to other products.{{sfn|Kitchin |Dodge|2011|pp=36-37}} | |||
| ===Licenses=== | |||
| Kinds of software by operation: ] as ], ] or ], ].--> | |||
| {{Main|Software license|Software copyright}} | |||
| ], a ] program]] | |||
| Source code is protected by ] that vests the owner with the exclusive right to copy the code. The underlying ideas or algorithms are not protected by copyright law, but are often treated as a ] and concealed by such methods as ]s.{{sfn|O'Regan|2022|pp=394-396}} ] has been recognized since the mid-1970s and is vested in the company that makes the software, not the employees or ]s who wrote it.{{sfn|O'Regan|2022|p=403}} The use of most software is governed by an agreement (]) between the copyright holder and the user. ] is usually sold under a restrictive license that limits copying and reuse (often enforced with tools such as ] (DRM)).{{sfn|O'Regan|2022|pp=394, 404}} ], in contrast, allow free use and redistribution of software with few conditions.{{sfn|O'Regan|2022|p=403}} Most open-source licenses used for software require that modifications be released under the same license, which can create complications when open-source software is reused in proprietary projects.{{sfn|Langer|2016|pp=44-45}} | |||
| ===Patents=== | |||
| === Quality and reliability === | |||
| {{ |
{{Main|Software patent|Software patent debate}} | ||
| ]s give an inventor an exclusive, time-limited license for a novel product or process.{{sfn|O'Regan|2022|p=395}} Ideas about what software could accomplish are not protected by law and concrete implementations are instead covered by ]. In some countries, a requirement for the claimed invention to have an effect on the physical world may also be part of the requirements for a software patent to be held valid.<ref>Gerardo Con Díaz, "The Text in the Machine: American Copyright Law and the Many Natures of Software, 1974–1978", ''Technology and Culture'' 57 (October 2016), 753–79.</ref> ]s have been ]. Before the 1998 case '']'', software patents were generally not recognized in the United States. In that case, the ] decided that business processes could be patented.{{sfn|Jones|2014|p=19}} Patent applications are complex and costly, and lawsuits involving patents can drive up the cost of products.{{sfn|O'Regan|2022|p=398}} Unlike copyrights, patents generally only apply in the jurisdiction where they were issued.{{sfn|O'Regan|2022|p=399}} | |||
| ==Impact== | |||
| Software quality is very important, especially for ] and system software like ], ] and ]. If software is faulty (buggy), it can delete a person's work, crash the computer and do other unexpected things. Faults and errors are called "]." Software is often also a victim to what is known as ], the progressive performance degradation resulting from a combination of unseen bugs. Many bugs are discovered and eliminated (debugged) through ]. However, software testing rarely – if ever – eliminates every bug; some programmers say that "every program has at least one more bug" (Lubarsky's Law).<ref>{{cite web|url=https://github.com/mark-watson/scripting-intelligence-book-examples/blob/master/part1/wikipedia_text/software.txt|title=scripting intelligence book examples}}</ref> All major software companies, such as Microsoft, Novell and ], have their own software testing departments with the specific goal of just testing. Software can be tested through ], ] and other methods, which are done manually, or most commonly, automatically, since the amount of code to be tested can be quite large. For instance, ] has extremely rigorous software testing procedures for many operating systems and communication functions. Many NASA-based operations interact and identify each other through command programs called software. This enables many people who work at NASA to check and evaluate functional systems overall. Programs containing command software enable hardware engineering and system operations to function much easier together. | |||
| {{further |Information Age}} | |||
| <!-- ] the man is using are actually ]s that require software to function.{{sfn|Kitchin |Dodge|2011|p=47}}{{sfn|Jones|2014|p=xxviii}}]] --> | |||
| ] | |||
| Engineer ] writes that "computers and software are making profound changes to every aspect of human life: education, work, warfare, entertainment, medicine, law, and everything else".{{sfn|Jones|2014|p=32}} It has become ubiquitous in ] in ].{{sfn|Kitchin |Dodge|2011|p=iv}} In many cases, software augments the functionality of existing technologies such as household ] and ]s.{{sfn|Kitchin |Dodge|2011|p=5}} Software also spawned entirely new technologies such as ], ], ], and ].{{sfn|Kitchin |Dodge|2011|p=5}}{{sfn|Jones|2014|p=xxviii}} New methods of communication, including ], ]s, ]s, ], ]s, and ], were enabled by the Internet.{{sfn|Manovich|2013|p=329}} Massive amounts of knowledge exceeding any paper-based library are now available with a quick ].{{sfn|Jones|2014|p=xxviii}} Most creative professionals have switched to software-based tools such as ], ], digital ], and ].{{sfn|Manovich|2013|p=333}} Almost every complex device is controlled by software.{{sfn|Jones|2014|p=xxviii}} | |||
| == |
==References== | ||
| {{reflist}} | |||
| {{main|Software license}} | |||
| ===Sources=== | |||
| The software's license gives the user the right to use the software in the licensed environment, and in the case of ]s, also grants other rights such as the right to make copies. | |||
| {{refbegin|indent=yes}} | |||
| *{{cite book |last1=Ablon |first1=Lillian |last2=Bogart |first2=Andy |title=Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits |date=2017 |publisher=Rand Corporation |isbn=978-0-8330-9761-3 |language=en|url=https://www.rand.org/content/dam/rand/pubs/research_reports/RR1700/RR1751/RAND_RR1751.pdf}} | |||
| ] can be divided into two types: | |||
| *{{cite book |last1=Anderson |first1=Thomas |last2=Dahlin |first2=Michael |author1-link=Thomas E. Anderson |title=Operating Systems: Principles and Practice |date=2014 |publisher=Recursive Books |isbn=978-0-9856735-2-9 |edition=2 |language=en}} | |||
| *{{cite book |last1=Campbell-Kelly |first1=Martin |last2=Garcia-Swartz |first2=Daniel D. |title=From Mainframes to Smartphones: A History of the International Computer Industry |date=2015 |publisher=Harvard University Press |isbn=978-0-674-28655-9 |language=en}} | |||
| * ], which includes the historical category ]. As the name suggests, freeware can be used for free, although in the case of shareware, this is sometimes only true for a limited period of time. However, the term shareware has fallen out of use, as the original name "shareware" was coined in a pre-internet age, and even larger, well-established software companies such as ] commonly offer free trial versions of some or all of their software. | |||
| *{{cite book |last1=Daswani |first1=Neil|authorlink=Neil Daswani |last2=Elbayadi |first2=Moudy |title=Big Breaches: Cybersecurity Lessons for Everyone |date=2021 |publisher=Apress |isbn=978-1-4842-6654-0}} | |||
| * software available for a fee, often inaccurately termed "commercial software", which can only be legally used on purchase of a license. | |||
| *{{Cite book |last=Dooley |first=John F. |title=Software Development, Design and Coding: With Patterns, Debugging, Unit Testing, and Refactoring |date=2017 |publisher=Apress |isbn=978-1-4842-3153-1 |language=en}} | |||
| *{{cite book |last1=Gabbrielli |first1=Maurizio |last2=Martini |first2=Simone |title=Programming Languages: Principles and Paradigms |date=2023 |publisher=Springer |isbn=978-3-031-34144-1 |language=en|edition=2nd}} | |||
| ], on the other hand, comes with a ], granting the recipient the rights to modify and redistribute the software. | |||
| *{{cite book |last1=Galin |first1=Daniel |title=Software Quality: Concepts and Practice |date=2018 |publisher=John Wiley & Sons |isbn=978-1-119-13449-7 |language=en}} | |||
| *{{cite book |last1=Haber |first1=Morey J. |last2=Hibbert |first2=Brad |title=Asset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect Organizations |date=2018 |publisher=Apress |isbn=978-1-4842-3627-7 |language=en}} | |||
| === Patents === | |||
| *{{cite book |last1=Jones |first1=Capers |title=The Technical and Social History of Software Engineering |date=2014 |publisher=Pearson Education |isbn=978-0-321-90342-6 |language=en}} | |||
| {{main|Software patent|Software patent debate}} | |||
| *{{cite book |last1=Kitchin |first1=Rob |last2=Dodge |first2=Martin |title=Code/space: Software and Everyday Life |date=2011 |publisher=MIT Press |isbn=978-0-262-04248-2 |language=en}} | |||
| *{{Cite book |last=Langer |first=Arthur M. |title=Guide to Software Development: Designing and Managing the Life Cycle |date=2016 |publisher=Springer |isbn=978-1-4471-6799-0 |language=en}} | |||
| Software patents, like other types of patents, are theoretically supposed to give an inventor an exclusive, time-limited license for a ''detailed idea (e.g. an algorithm) on how to implement'' a piece of software, or a component of a piece of software. Ideas for useful things that software could ''do'', and user ''requirements'', are not supposed to be patentable, and concrete implementations (i.e. the actual software packages implementing the patent) are not supposed to be patentable either - the latter are already covered by copyright, generally automatically. So software patents are supposed to cover the middle area, between requirements and concrete implementation. In some countries, a requirement for the claimed invention to have an effect on the physical world may also be part of the requirements for a software patent to be held valid - although since ''all'' useful software has effects on the physical world, this requirement may be open to debate. | |||
| *{{cite book |last1=Manovich |first1=Lev |title=Software Takes Command |date=2013 |publisher=Bloomsbury Academic |isbn=978-1-62356-745-3 |language=en}} | |||
| *{{cite book |last1=O'Regan |first1=Gerard |title=Concise Guide to Software Engineering: From Fundamentals to Application Methods |date=2022 |publisher=Springer Nature |isbn=978-3-031-07816-3 |language=en}} | |||
| Software patents are controversial in the software industry with many people holding different views about them. One of the sources of controversy is that the aforementioned split between initial ideas and patent does not seem to be honored in practice by patent lawyers - for example the patent for ] (AOP), which purported to claim rights over ''any'' programming tool implementing the idea of AOP, howsoever implemented. Another source of controversy is the effect on innovation, with many distinguished experts and companies arguing that software is such a fast-moving field that software patents merely create vast additional litigation costs and risks, and actually retard innovation. In the case of debates about software patents outside the US, the argument has been made that large American corporations and patent lawyers are likely to be the primary beneficiaries of allowing or continue to allow software patents. | |||
| *{{cite book |last1=Osterweil |first1=Leon J. |title=Perspectives on the Future of Software Engineering: Essays in Honor of Dieter Rombach |date=2013 |publisher=Springer |isbn=978-3-642-37395-4 |pages=237–254 |language=en |chapter=What Is Software? The Role of Empirical Methods in Answering the Question}} | |||
| *{{cite journal |last1=Rahman |first1=Hanif Ur |last2=da Silva |first2=Alberto Rodrigues |last3=Alzayed |first3=Asaad |last4=Raza |first4=Mushtaq |title=A Systematic Literature Review on Software Maintenance Offshoring Decisions |journal=Information and Software Technology |date=2024 |volume=172 |pages=107475 |doi=10.1016/j.infsof.2024.107475|ref={{sfnref|Rahman et al.|2024}}}} | |||
| == Design and implementation == | |||
| *{{cite book |last1=Reifer |first1=Donald J. |title=Software Maintenance Success Recipes |date=2012 |publisher=CRC Press |isbn=978-1-4398-5167-8 |language=en}} | |||
| {{main|Software development|Computer programming|Software engineering}} | |||
| *{{cite book |last1=Rosati |first1=Pierangelo |last2=Lynn |first2=Theo |title=Measuring the Business Value of Cloud Computing |date=2020 |publisher=Springer International Publishing |isbn=978-3-030-43198-3 |pages=19–37 |language=en |chapter=Measuring the Business Value of Infrastructure Migration to the Cloud}} | |||
| Design and implementation of software varies depending on the complexity of the software. For instance, design and creation of ] software will take much more time than designing and developing ] because of the difference in functionalities in each one. | |||
| * {{cite book |last1=Sebesta |first1=Robert W. |title=Concepts of Programming Languages |date=2012 |publisher=Addison-Wesley |isbn=978-0-13-139531-2 |edition=10 |language=en}} | |||
| *{{cite book |last1=Stull |first1=Edward |title=UX Fundamentals for Non-UX Professionals: User Experience Principles for Managers, Writers, Designers, and Developers |date=2018 |publisher=Apress |isbn=978-1-4842-3811-0 |language=en}} | |||
| Software is usually designed and created (coded/written/programmed) in ]s (IDE) like ], ] and ] that can simplify the process and ] the program. As noted in different section, software is usually created on top of existing software and the ] (API) that the underlying software provides like ], JavaBeans or ]. Libraries (APIs) are categorized for different purposes. For instance, ] library is used for designing ]s, ] library is used for designing graphical user interface (GUI) applications like ], and ] is used for designing ]s. Underlying ] ]s like ], ], ], and ] can be useful to creating software. When a program is designed, it relies on the API. For instance, if a user is designing a Microsoft Windows desktop application, he/she might use the ] Windows Forms library to design the desktop application and call its APIs like ''Form1.Close()'' and ''Form1.Show()''<ref>{{cite web |url=http://msdn.microsoft.com/en-us/library/default.aspx | title=MSDN Library|accessdate=2010-06-14}}</ref> to close or open the application and write the additional operations him/herself that it need to have. Without these APIs, the programmer needs to write these APIs him/herself. Companies like ], ], and ] provide their own APIs so that many applications are written using their ] that usually have numerous APIs in them. | |||
| *{{cite book |last1=Tanenbaum |first1=Andrew S.|authorlink=Andrew S. Tanenbaum |last2=Bos |first2=Herbert |title=Modern Operating Systems, Global Edition |date=2023 |publisher=Pearson Higher Ed |isbn=978-1-292-72789-9 |language=en}} | |||
| *{{cite book |last1=Tracy |first1=Kim W. |title=Software: A Technical History |date=2021 |publisher=Morgan & Claypool Publishers |isbn=978-1-4503-8724-8 |language=en}} | |||
| Computer software has special economic characteristics that make its design, creation, and distribution different from most other economic goods.{{Specify|Which characteristics?|date=May 2012}}<ref>{{cite journal|author=v. Engelhardt, Sebastian |year=2008|url=http://ideas.repec.org/p/jrp/jrpwrp/2008-045.html |title=The Economic Properties of Software|journal= Jena Economic Research Papers| volume= 2| issue= 2008–045.}} | |||
| *{{cite book |last1=Tripathy |first1=Priyadarshi |last2=Naik |first2=Kshirasagar |title=Software Evolution and Maintenance: A Practitioner's Approach |date=2014 |publisher=John Wiley & Sons |isbn=978-0-470-60341-3 |language=en}} | |||
| </ref><ref> | |||
| *{{Cite book |last=Tucker |first=Allen |title=Software Development: An Open Source Approach |last2=Morelli |first2=Ralph |last3=de Silva |first3=Chamindra |date=2011 |publisher=CRC Press |isbn=978-1-4398-8460-7 |language=en}} | |||
| {{cite web|url=http://dankaminsky.com/1999/03/02/69/ |title=Why Open Source Is The Optimum Economic Paradigm for Software|first= Dan |last=Kaminsky |year=1999}} | |||
| *{{cite journal |last1=Ulziit |first1=Bayarbuyan |last2=Warraich |first2=Zeeshan Akhtar |last3=Gencel |first3=Cigdem |last4=Petersen |first4=Kai |title=A conceptual framework of challenges and solutions for managing global software maintenance |journal=Journal of Software: Evolution and Process |date=2015 |volume=27 |issue=10 |pages=763–792 |doi=10.1002/smr.1720|ref={{sfnref|Ulziit et al.|2015}}}} | |||
| </ref> | |||
| *{{cite book |last1=Watt |first1=Andy |title=Building Modern SaaS Applications with C# And . NET: Build, Deploy, and Maintain Professional SaaS Applications |date=2023 |publisher=Packt |isbn=978-1-80461-087-9 |language=en}} | |||
| *{{cite book |last1=Varga |first1=Ervin |title=Unraveling Software Maintenance and Evolution: Thinking Outside the Box |date=2018 |publisher=Springer |isbn=978-3-319-71303-8 |language=en}} | |||
| A person who creates software is called a ], ] or ], terms that all have a similar meaning. | |||
| {{refend}} | |||
| == Industry and organizations == | |||
| {{main|Software industry}} | |||
| A great variety of software companies and programmers in the world comprise a software industry. Software can be quite a profitable industry: ], the founder of ] was the richest person in the world in 2009 largely due to his ownership of a significant number of shares in Microsoft, the company responsible for ] and ] software products. | |||
| Non-profit software organizations include the ], ] and ]. Software standard organizations like the ], ] develop software standards so that most software can interoperate through standards such as ], ] and ]. | |||
| Other well-known large software companies include ], ], ], ], ], and ], while small companies often provide innovation. | |||
| == See also == | |||
| * ] | |||
| * ] | |||
| {{portal bar|Software|Free software|Information technology}} | |||
| == References == | |||
| {{reflist}} | |||
| {{Software digital distribution platforms|state=collapsed}} | |||
| == External links == | |||
| {{subject bar|Free and open-source software|auto=1}} | |||
| {{Sister project links | wikt=software | commons=Special:Search/Software | b= | n= | s= | v=Computer Software | voy= |q=no}} | |||
| {{Authority control}} | |||
| * ] | |||
| * | |||
| * | |||
| {{DEFAULTSORT:Computer Software}} | |||
| ] | ] | ||
Latest revision as of 00:21, 24 November 2024
Instructions a computer can execute For other uses, see Software (disambiguation).

Software consists of computer programs that instruct the execution of a computer. Software also includes design documents and specifications.
The history of software is closely tied to the development of digital computers in the mid-20th century. Early programs were written in the machine language specific to the hardware. The introduction of high-level programming languages in 1958 allowed for more human-readable instructions, making software development easier and more portable across different computer architectures. Software in a programming language is run through a compiler or interpreter to execute on the architecture's hardware. Over time, software has become complex, owing to developments in networking, operating systems, and databases.
Software can generally be categorized into two main types:
- operating systems, which manage hardware resources and provide services for applications
- application software, which performs specific tasks for users
The rise of cloud computing has introduced the new software delivery model Software as a Service (SaaS). In SaaS, applications are hosted by a provider and accessed over the Internet.
The process of developing software involves several stages. The stages include software design, programming, testing, release, and maintenance. Software quality assurance and security are critical aspects of software development, as bugs and security vulnerabilities can lead to system failures and security breaches. Additionally, legal issues such as software licenses and intellectual property rights play a significant role in the distribution of software products.
History
Main article: History of software
The first use of the word software is credited to mathematician John Wilder Tukey in 1958. The first programmable computers, which appeared at the end of the 1940s, were programmed in machine language. Machine language is difficult to debug and not portable across different computers. Initially, hardware resources were more expensive than human resources. As programs became complex, programmer productivity became the bottleneck. The introduction of high-level programming languages in 1958 hid the details of the hardware and expressed the underlying algorithms into the code . Early languages include Fortran, Lisp, and COBOL.
Types
See also: Software categories
There are two main types of software:
- Operating systems are "the layer of software that manages a computer's resources for its users and their applications". There are three main purposes that an operating system fulfills:
- Allocating resources between different applications, deciding when they will receive central processing unit (CPU) time or space in memory.
- Providing an interface that abstracts the details of accessing hardware details (like physical memory) to make things easier for programmers.
- Offering common services, such as an interface for accessing network and disk devices. This enables an application to be run on different hardware without needing to be rewritten.
- Application software runs on top of the operating system and uses the computer's resources to perform a task. There are many different types of application software because the range of tasks that can be performed with modern computers is so large. Applications account for most software and require the environment provided by an operating system, and often other applications, in order to function.
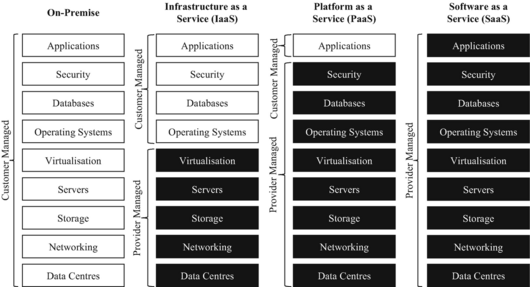
Software can also be categorized by how it is deployed. Traditional applications are purchased with a perpetual license for a specific version of the software, downloaded, and run on hardware belonging to the purchaser. The rise of the Internet and cloud computing enabled a new model, software as a service (SaaS), in which the provider hosts the software (usually built on top of rented infrastructure or platforms) and provides the use of the software to customers, often in exchange for a subscription fee. By 2023, SaaS products—which are usually delivered via a web application—had become the primary method that companies deliver applications.
Software development and maintenance

Software companies aim to deliver a high-quality product on time and under budget. A challenge is that software development effort estimation is often inaccurate. Software development begins by conceiving the project, evaluating its feasibility, analyzing the business requirements, and making a software design. Most software projects speed up their development by reusing or incorporating existing software, either in the form of commercial off-the-shelf (COTS) or open-source software. Software quality assurance is typically a combination of manual code review by other engineers and automated software testing. Due to time constraints, testing cannot cover all aspects of the software's intended functionality, so developers often focus on the most critical functionality. Formal methods are used in some safety-critical systems to prove the correctness of code, while user acceptance testing helps to ensure that the product meets customer expectations. There are a variety of software development methodologies, which vary from completing all steps in order to concurrent and iterative models. Software development is driven by requirements taken from prospective users, as opposed to maintenance, which is driven by events such as a change request.
Frequently, software is released in an incomplete state when the development team runs out of time or funding. Despite testing and quality assurance, virtually all software contains bugs where the system does not work as intended. Post-release software maintenance is necessary to remediate these bugs when they are found and keep the software working as the environment changes over time. New features are often added after the release. Over time, the level of maintenance becomes increasingly restricted before being cut off entirely when the product is withdrawn from the market. As software ages, it becomes known as legacy software and can remain in use for decades, even if there is no one left who knows how to fix it. Over the lifetime of the product, software maintenance is estimated to comprise 75 percent or more of the total development cost.
Completing a software project involves various forms of expertise, not just in software programmers but also testing, documentation writing, project management, graphic design, user experience, user support, marketing, and fundraising.
Quality and security
Main articles: Software quality and Computer securitySoftware quality is defined as meeting the stated requirements as well as customer expectations. Quality is an overarching term that can refer to a code's correct and efficient behavior, its reusability and portability, or the ease of modification. It is usually more cost-effective to build quality into the product from the beginning rather than try to add it later in the development process. Higher quality code will reduce lifetime cost to both suppliers and customers as it is more reliable and easier to maintain. Software failures in safety-critical systems can be very serious including death. By some estimates, the cost of poor quality software can be as high as 20 to 40 percent of sales. Despite developers' goal of delivering a product that works entirely as intended, virtually all software contains bugs.
The rise of the Internet also greatly increased the need for computer security as it enabled malicious actors to conduct cyberattacks remotely. If a bug creates a security risk, it is called a vulnerability. Software patches are often released to fix identified vulnerabilities, but those that remain unknown (zero days) as well as those that have not been patched are still liable for exploitation. Vulnerabilities vary in their ability to be exploited by malicious actors, and the actual risk is dependent on the nature of the vulnerability as well as the value of the surrounding system. Although some vulnerabilities can only be used for denial of service attacks that compromise a system's availability, others allow the attacker to inject and run their own code (called malware), without the user being aware of it. To thwart cyberattacks, all software in the system must be designed to withstand and recover from external attack. Despite efforts to ensure security, a significant fraction of computers are infected with malware.
Encoding and execution
Programming languages
Main article: Programming language
Programming languages are the format in which software is written. Since the 1950s, thousands of different programming languages have been invented; some have been in use for decades, while others have fallen into disuse. Some definitions classify machine code—the exact instructions directly implemented by the hardware—and assembly language—a more human-readable alternative to machine code whose statements can be translated one-to-one into machine code—as programming languages. Programs written in the high-level programming languages used to create software share a few main characteristics: knowledge of machine code is not necessary to write them, they can be ported to other computer systems, and they are more concise and human-readable than machine code. They must be both human-readable and capable of being translated into unambiguous instructions for computer hardware.
Compilation, interpretation, and execution
The invention of high-level programming languages was simultaneous with the compilers needed to translate them automatically into machine code. Most programs do not contain all the resources needed to run them and rely on external libraries. Part of the compiler's function is to link these files in such a way that the program can be executed by the hardware. Once compiled, the program can be saved as an object file and the loader (part of the operating system) can take this saved file and execute it as a process on the computer hardware. Some programming languages use an interpreter instead of a compiler. An interpreter converts the program into machine code at run time, which makes them 10 to 100 times slower than compiled programming languages.
Legal issues
Liability
Main article: Software product liabilitySoftware is often released with the knowledge that it is incomplete or contains bugs. Purchasers knowingly buy it in this state, which has led to a legal regime where liability for software products is significantly curtailed compared to other products.
Licenses
Main articles: Software license and Software copyright
Source code is protected by copyright law that vests the owner with the exclusive right to copy the code. The underlying ideas or algorithms are not protected by copyright law, but are often treated as a trade secret and concealed by such methods as non-disclosure agreements. Software copyright has been recognized since the mid-1970s and is vested in the company that makes the software, not the employees or contractors who wrote it. The use of most software is governed by an agreement (software license) between the copyright holder and the user. Proprietary software is usually sold under a restrictive license that limits copying and reuse (often enforced with tools such as digital rights management (DRM)). Open-source licenses, in contrast, allow free use and redistribution of software with few conditions. Most open-source licenses used for software require that modifications be released under the same license, which can create complications when open-source software is reused in proprietary projects.
Patents
Main articles: Software patent and Software patent debatePatents give an inventor an exclusive, time-limited license for a novel product or process. Ideas about what software could accomplish are not protected by law and concrete implementations are instead covered by copyright law. In some countries, a requirement for the claimed invention to have an effect on the physical world may also be part of the requirements for a software patent to be held valid. Software patents have been historically controversial. Before the 1998 case State Street Bank & Trust Co. v. Signature Financial Group, Inc., software patents were generally not recognized in the United States. In that case, the Supreme Court decided that business processes could be patented. Patent applications are complex and costly, and lawsuits involving patents can drive up the cost of products. Unlike copyrights, patents generally only apply in the jurisdiction where they were issued.
Impact
Further information: Information Age
Engineer Capers Jones writes that "computers and software are making profound changes to every aspect of human life: education, work, warfare, entertainment, medicine, law, and everything else". It has become ubiquitous in everyday life in developed countries. In many cases, software augments the functionality of existing technologies such as household appliances and elevators. Software also spawned entirely new technologies such as the Internet, video games, mobile phones, and GPS. New methods of communication, including email, forums, blogs, microblogging, wikis, and social media, were enabled by the Internet. Massive amounts of knowledge exceeding any paper-based library are now available with a quick web search. Most creative professionals have switched to software-based tools such as computer-aided design, 3D modeling, digital image editing, and computer animation. Almost every complex device is controlled by software.
References
- Stair, Ralph M. (2003). Principles of Information Systems, Sixth Edition. Thomson. p. 16. ISBN 0-619-06489-7.
Software consists of computer programs that govern the operation of the computer.
- Jones 2014, pp. 19, 22.
- Tracy 2021, p. 2.
- Gabbrielli & Martini 2023, p. 519.
- Gabbrielli & Martini 2023, pp. 520–521.
- Gabbrielli & Martini 2023, p. 522.
- Gabbrielli & Martini 2023, p. 521.
- ^ Tracy 2021, p. 1.
- Anderson & Dahlin 2014, p. 6.
- ^ Anderson & Dahlin 2014, p. 7.
- Tanenbaum & Bos 2023, p. 5.
- Anderson & Dahlin 2014, pp. 7, 9, 13.
- Anderson & Dahlin 2014, pp. 6–7.
- Jones 2014, p. 121.
- Tracy 2021, p. 66.
- Tracy 2021, p. 72.
- ^ O'Regan 2022, p. 386.
- Campbell-Kelly & Garcia-Swartz 2015, pp. 156–157.
- Rosati & Lynn 2020, p. 23.
- Watt 2023, p. 4.
- O'Regan 2022, p. 7.
- O'Regan 2022, p. 5.
- ^ Dooley 2017, p. 1.
- O'Regan 2022, pp. 18, 110–111.
- Tracy 2021, pp. 43, 76.
- O'Regan 2022, pp. 117–118.
- O'Regan 2022, p. 54.
- O'Regan 2022, p. 267.
- O'Regan 2022, p. 20.
- O'Regan 2022, p. 9.
- Tripathy & Naik 2014, p. 26.
- Reifer 2012, p. 22.
- Tripathy & Naik 2014, pp. 4, 27.
- Tripathy & Naik 2014, p. 89.
- Tracy 2021, p. 3.
- Varga 2018, p. 6.
- Ulziit et al. 2015, p. 764.
- Tucker, Morelli & de Silva 2011, p. 7.
- Stull 2018, pp. 24–25.
- Galin 2018, p. 3.
- Galin 2018, p. 26.
- O'Regan 2022, pp. 68, 117.
- ^ O'Regan 2022, pp. 3, 268.
- Varga 2018, p. 12.
- O'Regan 2022, p. 119.
- Ablon & Bogart 2017, p. 1.
- Campbell-Kelly & Garcia-Swartz 2015, p. 164.
- ^ O'Regan 2022, p. 266.
- ^ Ablon & Bogart 2017, p. 2.
- Daswani & Elbayadi 2021, p. 25.
- Daswani & Elbayadi 2021, pp. 26–27.
- Haber & Hibbert 2018, pp. 5–6.
- Kitchin & Dodge 2011, p. 37.
- Tracy 2021, p. 117.
- Tracy 2021, pp. 118–120.
- Tracy 2021, pp. 118–119.
- Kitchin & Dodge 2011, p. 26.
- Tracy 2021, p. 121.
- Tracy 2021, pp. 122–123.
- O'Regan 2022, p. 375.
- Sebesta 2012, p. 28.
- Kitchin & Dodge 2011, pp. 36–37.
- O'Regan 2022, pp. 394–396.
- ^ O'Regan 2022, p. 403.
- O'Regan 2022, pp. 394, 404.
- Langer 2016, pp. 44–45.
- O'Regan 2022, p. 395.
- Gerardo Con Díaz, "The Text in the Machine: American Copyright Law and the Many Natures of Software, 1974–1978", Technology and Culture 57 (October 2016), 753–79.
- Jones 2014, p. 19.
- O'Regan 2022, p. 398.
- O'Regan 2022, p. 399.
- ^ Manovich 2013, p. 333.
- Jones 2014, p. 32.
- Kitchin & Dodge 2011, p. iv.
- ^ Kitchin & Dodge 2011, p. 5.
- ^ Jones 2014, p. xxviii.
- Manovich 2013, p. 329.
Sources
- Ablon, Lillian; Bogart, Andy (2017). Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits (PDF). Rand Corporation. ISBN 978-0-8330-9761-3.
- Anderson, Thomas; Dahlin, Michael (2014). Operating Systems: Principles and Practice (2 ed.). Recursive Books. ISBN 978-0-9856735-2-9.
- Campbell-Kelly, Martin; Garcia-Swartz, Daniel D. (2015). From Mainframes to Smartphones: A History of the International Computer Industry. Harvard University Press. ISBN 978-0-674-28655-9.
- Daswani, Neil; Elbayadi, Moudy (2021). Big Breaches: Cybersecurity Lessons for Everyone. Apress. ISBN 978-1-4842-6654-0.
- Dooley, John F. (2017). Software Development, Design and Coding: With Patterns, Debugging, Unit Testing, and Refactoring. Apress. ISBN 978-1-4842-3153-1.
- Gabbrielli, Maurizio; Martini, Simone (2023). Programming Languages: Principles and Paradigms (2nd ed.). Springer. ISBN 978-3-031-34144-1.
- Galin, Daniel (2018). Software Quality: Concepts and Practice. John Wiley & Sons. ISBN 978-1-119-13449-7.
- Haber, Morey J.; Hibbert, Brad (2018). Asset Attack Vectors: Building Effective Vulnerability Management Strategies to Protect Organizations. Apress. ISBN 978-1-4842-3627-7.
- Jones, Capers (2014). The Technical and Social History of Software Engineering. Pearson Education. ISBN 978-0-321-90342-6.
- Kitchin, Rob; Dodge, Martin (2011). Code/space: Software and Everyday Life. MIT Press. ISBN 978-0-262-04248-2.
- Langer, Arthur M. (2016). Guide to Software Development: Designing and Managing the Life Cycle. Springer. ISBN 978-1-4471-6799-0.
- Manovich, Lev (2013). Software Takes Command. Bloomsbury Academic. ISBN 978-1-62356-745-3.
- O'Regan, Gerard (2022). Concise Guide to Software Engineering: From Fundamentals to Application Methods. Springer Nature. ISBN 978-3-031-07816-3.
- Osterweil, Leon J. (2013). "What Is Software? The Role of Empirical Methods in Answering the Question". Perspectives on the Future of Software Engineering: Essays in Honor of Dieter Rombach. Springer. pp. 237–254. ISBN 978-3-642-37395-4.
- Rahman, Hanif Ur; da Silva, Alberto Rodrigues; Alzayed, Asaad; Raza, Mushtaq (2024). "A Systematic Literature Review on Software Maintenance Offshoring Decisions". Information and Software Technology. 172: 107475. doi:10.1016/j.infsof.2024.107475.
- Reifer, Donald J. (2012). Software Maintenance Success Recipes. CRC Press. ISBN 978-1-4398-5167-8.
- Rosati, Pierangelo; Lynn, Theo (2020). "Measuring the Business Value of Infrastructure Migration to the Cloud". Measuring the Business Value of Cloud Computing. Springer International Publishing. pp. 19–37. ISBN 978-3-030-43198-3.
- Sebesta, Robert W. (2012). Concepts of Programming Languages (10 ed.). Addison-Wesley. ISBN 978-0-13-139531-2.
- Stull, Edward (2018). UX Fundamentals for Non-UX Professionals: User Experience Principles for Managers, Writers, Designers, and Developers. Apress. ISBN 978-1-4842-3811-0.
- Tanenbaum, Andrew S.; Bos, Herbert (2023). Modern Operating Systems, Global Edition. Pearson Higher Ed. ISBN 978-1-292-72789-9.
- Tracy, Kim W. (2021). Software: A Technical History. Morgan & Claypool Publishers. ISBN 978-1-4503-8724-8.
- Tripathy, Priyadarshi; Naik, Kshirasagar (2014). Software Evolution and Maintenance: A Practitioner's Approach. John Wiley & Sons. ISBN 978-0-470-60341-3.
- Tucker, Allen; Morelli, Ralph; de Silva, Chamindra (2011). Software Development: An Open Source Approach. CRC Press. ISBN 978-1-4398-8460-7.
- Ulziit, Bayarbuyan; Warraich, Zeeshan Akhtar; Gencel, Cigdem; Petersen, Kai (2015). "A conceptual framework of challenges and solutions for managing global software maintenance". Journal of Software: Evolution and Process. 27 (10): 763–792. doi:10.1002/smr.1720.
- Watt, Andy (2023). Building Modern SaaS Applications with C# And . NET: Build, Deploy, and Maintain Professional SaaS Applications. Packt. ISBN 978-1-80461-087-9.
- Varga, Ervin (2018). Unraveling Software Maintenance and Evolution: Thinking Outside the Box. Springer. ISBN 978-3-319-71303-8.
 Media from Commons
Media from Commons News from Wikinews
News from Wikinews Quotations from Wikiquote
Quotations from Wikiquote Textbooks from Wikibooks
Textbooks from Wikibooks Resources from Wikiversity
Resources from Wikiversity