| Revision as of 10:05, 27 April 2010 view sourceWtsao (talk | contribs)190 edits reverted vandalism by SamJohnston. Warned him not to mass undo changes on the talk page. That kind of behavior is unproductive. Someone with his COI should be more careful.← Previous edit | Latest revision as of 01:35, 8 January 2025 view source SdkbBot (talk | contribs)Bots357,396 editsm Removed erroneous space and general fixes (task 1)Tag: AWB | ||
| Line 1: | Line 1: | ||
| {{Short description|Form of shared internet-based computing}} | |||
| {{pp-move-vandalism|small=yes}} | |||
| {{Redirect-distinguish|Cloud Computing|Cloud Computing (horse)}} | |||
| {{internet hosting}} | |||
| {{pp-move}} | |||
| '''Cloud computing''' is ]-based ], whereby shared resources, software and information are provided to computers and other devices on-demand, similar to a public utility such as the electricity grid.<!-- per consensus on talk page: http://en.wikipedia.org/search/?title=Talk:Cloud_computing&oldid=349182637#The_lead.27s_first_sentence --> | |||
| {{protection padlock|small=y}} | |||
| {{Prone to spam|date=January 2017}} | |||
| Details are abstracted from the users who no longer have need of, expertise in, or control over the technology infrastructure "in the cloud" that supports them.<ref></ref> Cloud computing describes a new supplement, consumption and delivery model for IT services based on the Internet, and it typically involves the provision of dynamically ] and often ] resources as a service over the ].<ref name="gartner"></ref><ref name="really">{{cite web|url=http://www.infoworld.com/d/cloud-computing/what-cloud-computing-really-means-031|title=What cloud computing really means|last=Gruman|first=Galen|date=2008-04-07|work=]|accessdate=2009-06-02}}</ref> It is a byproduct and consequence of the ease-of-access to remote ] sites provided by the Internet.<ref>{{cite web|url=http://www.economist.com/displaystory.cfm?story_id=14637206|title=Cloud Computing: Clash of the clouds|date=2009-10-15|publisher=The Economist|accessdate=2009-11-03}}</ref> | |||
| {{Use American English|date=April 2020}} | |||
| ] | |||
| The term ''cloud'' is used as a ] for the Internet, based on the cloud drawing used in the past to represent the telephone network,<ref>http://www.sellsbrothers.com/writing/intro2tapi/default.aspx?content=pstn.htm</ref> and later to depict the Internet in ]s as an ] of the underlying infrastructure it represents.<ref></ref> Typical cloud computing providers deliver common ]s online which are accessed from another web service or software like a ], while the ] and ] are stored on ]. | |||
| "Cloud computing is a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to ].<ref name=":0">{{Cite news |date=2023 |title=ISO/IEC 22123-1:2023(E) - Information technology - Cloud computing - Part 1: Vocabulary |work=International Organization for Standardization}}</ref> | |||
| Most cloud computing infrastructure consists of reliable services delivered through ]s and built on servers. Clouds often appear as single points of access for all consumers' computing needs. Commercial offerings are generally expected to meet ] (QoS) requirements of customers and typically offer ].<ref name="ccpaper">{{cite paper | |||
| | first = Rajkumar |last=Buyya | |||
| |coauthors= Chee Shin Yeo, Srikumar Venugopal | |||
| | title = Market-Oriented Cloud Computing: Vision, Hype, and Reality for Delivering IT Services as Computing Utilities | |||
| | pages = 9 | |||
| | publisher = Department of Computer Science and Software Engineering, The University of Melbourne, Australia | |||
| | url = http://www.gridbus.org/~raj/papers/hpcc2008_keynote_cloudcomputing.pdf | |||
| | format = ] | |||
| | accessdate = 2008-07-31 | |||
| }}</ref> | |||
| ==Essential Characteristics== | |||
| == Criticism of the term== | |||
| In 2011, the ] (NIST) identified five "essential characteristics" for cloud systems.<ref name="nist">{{cite tech report|title=The NIST Definition of Cloud Computing|number=Special publication 800-145|institution=National Institute of Standards and Technology: U.S. Department of Commerce|date=September 2011|author1=Mell, Peter|author2=Timothy Grance|doi=10.6028/NIST.SP.800-145}}</ref> Below are the exact definitions according to NIST:<ref name="nist" /> | |||
| {{Criticism section|date=March 2010}} <!-- please do not remove this template unless you address the problem, such as by making the article more balanced by integrating this criticism and removing the need for the section --> | |||
| * '''On-demand self-service:''' "A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service provider." | |||
| * '''Broad network access:''' "Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, tablets, ]s, and workstations)." | |||
| * ''']:''' " The provider's computing resources are pooled to serve multiple consumers using a multi-tenant model, with different physical and virtual resources dynamically assigned and reassigned according to consumer demand." | |||
| * '''Rapid elasticity:''' "Capabilities can be elastically provisioned and released, in some cases automatically, to scale rapidly outward and inward commensurate with demand. To the consumer, the capabilities available for provisioning often appear unlimited and can be appropriated in any quantity at any time." | |||
| * '''Measured service:''' "Cloud systems automatically control and optimize resource use by leveraging a metering capability at some level of abstraction appropriate to the type of service (e.g., storage, processing, bandwidth, and active user accounts). Resource usage can be monitored, controlled, and reported, providing transparency for both the provider and consumer of the utilized service. | |||
| By 2023, the ] (ISO) had expanded and refined the list.<ref name=":1" /> | |||
| ==History== | |||
| ], founder of the Free Software Foundation and creator of the computer operating system GNU, said that cloud computing was simply a trap aimed at forcing more people to buy into locked, proprietary systems that would cost them more and more over time. | |||
| {{main|History of cloud computing}} | |||
| "It's stupidity. It's worse than stupidity: it's a marketing hype campaign," he told The Guardian. | |||
| The history of cloud computing extends back to the 1960s, with the initial concepts of time-sharing becoming popularized via ] (RJE). The "data center" model, where users submitted jobs to operators to run on mainframes, was predominantly used during this era. This was a time of exploration and experimentation with ways to make large-scale computing power available to more users through ], optimizing the infrastructure, platform, and applications, and increasing efficiency for end users.{{ref RFC|105}} | |||
| "Somebody is saying this is inevitable – and whenever you hear somebody saying that, it's very likely to be a set of businesses campaigning to make it true." | |||
| <ref name="rms08"> ], Monday 29 September 2008 14.11 BST</ref> | |||
| The "cloud" metaphor for virtualized services dates to 1994, when it was used by ] for the universe of "places" that mobile agents in the ] environment could "go". The metaphor is credited to David Hoffman, a General Magic communications specialist, based on its long-standing use in networking and telecom.<ref>{{cite magazine |last=Levy |first=Steven |date=April 1994 |url=http://archive.wired.com/wired/archive/2.04/general.magic_pr.html |title=Bill and Andy's Excellent Adventure II |archive-url=https://web.archive.org/web/20151002033751/http://archive.wired.com/wired/archive/2.04/general.magic_pr.html |archive-date=2015-10-02 |magazine=Wired}}</ref> The expression ''cloud computing'' became more widely known in 1996 when ] drew up a ] for future computing and the ]. The company's ambition was to supercharge ] with "cloud computing-enabled applications". The business plan foresaw that online consumer file storage would likely be commercially successful. As a result, Compaq decided to sell ] hardware to ]s.<ref>{{Cite book|title= To the Cloud: Big Data in a Turbulent World |url=https://books.google.com/books?id=YwbvCgAAQBAJ&pg=PA15 | author1=Mosco, Vincent |publisher= Taylor & Francis |year=2015 |isbn= 9781317250388 | pages=15}}</ref> | |||
| ], CEO of ] has stated that cloud computing has been defined as "everything that we already do" and that it will have no effect except to "change the wording on some of our ads"<ref name="ellisonhell"></ref><ref name="ellisonnail"></ref>. ] has since launched a cloud computing center and worldwide tour. ] Principal Analyst John Rymer dismisses Ellison's remarks by stating that his "comments are complete nonsense and he knows it". <ref></ref><ref></ref><ref></ref> | |||
| In the 2000s, the application of cloud computing began to take shape with the establishment of ] (AWS) in 2002, which allowed developers to build applications independently. In 2006 Amazon Simple Storage Service, known as ], and the ] (EC2) were released. In 2008 ]'s development of the first ] for deploying private and hybrid clouds.<ref>{{cite web |url=https://aws.amazon.com/about-aws/whats-new/2006/08/24/announcing-amazon-elastic-compute-cloud-amazon-ec2---beta/ |title=Announcing Amazon Elastic Compute Cloud (Amazon EC2) – beta |date=24 August 2006 |access-date=31 May 2014 |archive-date=13 August 2014 |archive-url=https://web.archive.org/web/20140813195808/http://aws.amazon.com/about-aws/whats-new/2006/08/24/announcing-amazon-elastic-compute-cloud-amazon-ec2---beta/ |url-status=live }}</ref><ref>{{cite web |last1=Qian |first1=Ling |last2=Lou |first2=Zhigou |last3=Du |first3=Yujian |last4=Gou |first4=Leitao |title=Cloud Computing: An Overview |url=https://www.researchgate.net/publication/221276709 |access-date=19 April 2021}}</ref> | |||
| During a video interview, ] VP Frank Gillett expresses criticism about the nature of and motivations behind the push for cloud computing. He describes what he calls "cloud washing" in the industry whereby companies relabel their products as cloud computing resulting in a lot of marketing innovation on top of real innovation. The result is a lot of overblown hype surrounding cloud computing. Gillett sees cloud computing as revolutionary in the long term but over-hyped and misunderstood in the short term, representing more of a gradual shift in our thinking about computer systems and not a sudden transformational change.<ref></ref><ref></ref> | |||
| The following decade saw the launch of various cloud services. In 2010, ] launched ], and ] and ] initiated an open-source cloud-software project, ]. ] introduced the ] framework in 2011, and ] announced the ] in 2012. In December 2019, Amazon launched AWS Outposts, a service that extends AWS infrastructure, services, ]s, and tools to customer data centers, co-location spaces, or on-premises facilities.<ref name="Azure">{{cite web |url=http://blogs.technet.com/b/microsoft_blog/archive/2010/02/01/windows-azure-general-availability.aspx |title=Windows Azure General Availability |work=The Official Microsoft Blog |publisher=Microsoft |date=2010-02-01 |access-date=2015-05-03 |archive-url=https://web.archive.org/web/20140511230956/http://blogs.technet.com/b/microsoft_blog/archive/2010/02/01/windows-azure-general-availability.aspx |archive-date=2014-05-11 |url-status=dead }}</ref><ref>{{cite web|url=https://aws.amazon.com/about-aws/whats-new/2019/12/announcing-general-availability-of-aws-outposts/|title=Announcing General Availability of AWS Outposts|website=Amazon Web Services, Inc.|access-date=2021-02-04|archive-date=2021-01-21|archive-url=https://web.archive.org/web/20210121002254/https://aws.amazon.com/about-aws/whats-new/2019/12/announcing-general-availability-of-aws-outposts/|url-status=live}}</ref> | |||
| ==Comparisons== | |||
| <!-- this need not enumerate every different type of computing, just the top 1/2 dozen that are provably linked to cloud computing --> | |||
| Cloud computing derives characteristics from, but should not be confused with: | |||
| #] — "computer systems capable of ]".<ref></ref> | |||
| # ] – ''Client–server computing'' refers broadly to any ] that distinguishes between service providers (servers) and service requesters (clients).<ref>{{cite web|url=http://java.sun.com/developer/Books/jdbc/ch07.pdf|publisher=Sun Microsystem|title=Distributed Application Architecture|accessdate=2009-06-16}}</ref> | |||
| #] — "a form of ] and ], whereby a 'super and virtual computer' is composed of a ] of networked, ] computers acting in concert to perform very large tasks" | |||
| #] — powerful ]s used mainly by large organizations for critical applications, typically bulk data processing such as ], industry and consumer statistics, ], and financial ].<ref></ref> | |||
| #] — the "packaging of ], such as computation and storage, as a metered service similar to a traditional ], such as ]";<ref name="It's probable that you’ve misunderstood “Cloud Computing” till now">{{cite web|url=http://portal.acm.org/citation.cfm?id=1496091.1496100&coll=&dl=ACM&CFID=21518680&CFTOKEN=18800807|title=It's probable that you’ve misunderstood 'Cloud Computing' until now|publisher=TechPluto}}</ref> | |||
| #] – systems in which data transfer utilizes the shared resources of every system attached to the ], setup for a specific task or purpose (ie: ] as one example of many that exist.) | |||
| == Value proposition == | |||
| ==Characteristics== | |||
| Cloud computing can enable shorter time to market by providing pre-configured tools, scalable resources, and managed services, allowing users to focus on their core business value instead of maintaining infrastructure. Cloud platforms can enable organizations and individuals to reduce upfront capital expenditures on physical infrastructure by shifting to an operational expenditure model, where costs scale with usage. Cloud platforms also offer managed services and tools, such as artificial intelligence, data analytics, and machine learning, which might otherwise require significant in-house expertise and infrastructure investment.<ref name=":7">{{Cite book |title=Cloud Computing: Concepts, Technology & Architecture |isbn=978-0133387520}}</ref><ref name=":8">{{Cite book |title=Cloud Computing, revised and updated edition |isbn=978-0262546478}}</ref><ref name=":9">{{Cite book |title=Cloud Computing |isbn=978-1284233971}}</ref> | |||
| In general, cloud computing customers do not own the physical infrastructure, instead avoiding ] by renting usage from a third-party provider. Sharing "perishable and intangible" computing power among ] can improve utilization rates, as servers are not unnecessarily left idle (which can reduce costs significantly while increasing the speed of application development). A side-effect of this approach is that overall computer usage rises dramatically, as customers do not have to engineer for peak load limits.<ref name="wpcarney"></ref> The same goes to networking resources, such as ]. | |||
| While cloud computing can offer cost advantages through effective resource optimization, organizations often face challenges such as unused resources, inefficient configurations, and hidden costs without proper oversight and governance. Many cloud platforms provide cost management tools, such as AWS Cost Explorer and Azure Cost Management, and frameworks like FinOps have emerged to standardize financial operations in the cloud. Cloud computing also facilitates collaboration, remote work, and global service delivery by enabling secure access to data and applications from any location with an internet connection.<ref name=":7" /><ref name=":8" /><ref name=":9" /> | |||
| ===Economics=== | |||
| Cloud computing users can avoid ] (CapEx) on hardware, software, and services when they pay a provider only for what they use. Consumption is usually billed on a ] (resources consumed, like electricity) or ] (time-based, like a newspaper) basis with little or no upfront cost. Other benefits of this ]-style approach are low ], shared infrastructure and costs, low management overhead, and immediate access to a broad range of applications. In general, users can terminate the contract at any time (thereby avoiding ] risk and uncertainty), and the services are often covered by ]s (SLAs) with financial penalties.<ref></ref><ref></ref> | |||
| Cloud providers offer various redundancy options for core services, such as managed storage and managed databases, though redundancy configurations often vary by service tier. Advanced redundancy strategies, such as cross-region replication or failover systems, typically require explicit configuration and may incur additional costs or licensing fees.<ref name=":7" /><ref name=":8" /><ref name=":9" /> | |||
| According to ], the strategic importance of ] is diminishing as it becomes standardized and less expensive. He argues that the cloud computing ] is similar to the displacement of ]s by ]s early in the 20th century.<ref></ref> | |||
| Cloud environments operate under a shared responsibility model, where providers are typically responsible for infrastructure security, physical hardware, and software updates, while customers are accountable for data encryption, identity and access management (IAM), and application-level security. These responsibilities vary depending on the cloud service model—Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS)—with customers typically having more control and responsibility in IaaS environments and progressively less in PaaS and SaaS models, often trading control for convenience and managed services.<ref name=":7" /><ref name=":8" /><ref name=":9" /> | |||
| Although companies might be able to save on upfront capital expenditures, they might not save much and might actually pay more for operating expenses. In situations where the capital expense would be relatively small, or where the organization has more flexibility in their capital budget than their operating budget, the cloud model might not make great fiscal sense. Other factors impacting the scale of any potential cost savings include the efficiency of a company’s data center as compared to the cloud vendor’s, the company's existing operating costs, the level of adoption of cloud computing, and the type of functionality being hosted in the cloud.<ref></ref><ref></ref> | |||
| == Factors Influencing Adoption and Suitability of Cloud Computing == | |||
| Among the items that some cloud hosts charge for are ]s (often with extra charges for high-memory or high-CPU instances); data transfer in and out; storage (measured by the GB-month); ]s; ]s and ]s; ]es; and ]. In some cases, users can bid on instances, with pricing dependent on demand for available instances. | |||
| The decision to adopt cloud computing or maintain on-premises infrastructure depends on factors such as scalability, cost structure, latency requirements, regulatory constraints, and infrastructure customization.<ref name=":3">{{Cite book |title=Cloud Computing For Dummies |isbn=978-0470484708}}</ref><ref name=":4">{{Cite book |title=Hybrid Cloud for Architects: Build robust hybrid cloud solutions using AWS and OpenStack |isbn=9781788623513}}</ref><ref name=":5">{{Cite book |title=Security Architecture for Hybrid Cloud: A Practical Method for Designing Security Using Zero Trust Principles |isbn=9781098157777}}</ref><ref name=":6">{{Cite book |title=Architecting the Cloud: Design Decisions for Cloud Computing Service Models (SaaS, PaaS, and IaaS) |isbn=978-1118617618}}</ref> | |||
| Organizations with variable or unpredictable workloads, limited capital for upfront investments, or a focus on rapid scalability benefit from cloud adoption. Startups, SaaS companies, and e-commerce platforms often prefer the pay-as-you-go operational expenditure (OpEx) model of cloud infrastructure. Additionally, companies prioritizing global accessibility, remote workforce enablement, disaster recovery, and leveraging advanced services such as AI/ML and analytics are well-suited for the cloud. In recent years, some cloud providers have started offering specialized services for high-performance computing and low-latency applications, addressing some use cases previously exclusive to on-premises setups.<ref name=":3" /><ref name=":4" /><ref name=":5" /><ref name=":6" /> | |||
| === Architecture === | |||
| ] | |||
| On the other hand, organizations with strict regulatory requirements, highly predictable workloads, or reliance on deeply integrated legacy systems may find cloud infrastructure less suitable. Businesses in industries like defense, government, or those handling highly sensitive data often favor on-premises setups for greater control and data sovereignty. Additionally, companies with ultra-low latency requirements, such as high-frequency trading (HFT) firms, rely on custom hardware (e.g., FPGAs) and physical proximity to exchanges, which most cloud providers cannot fully replicate despite recent advancements. Similarly, tech giants like Google, Meta, and Amazon build their own data centers due to economies of scale, predictable workloads, and the ability to customize hardware and network infrastructure for optimal efficiency. However, these companies also use cloud services selectively for certain workloads and applications where it aligns with their operational needs.<ref name=":3" /><ref name=":4" /><ref name=":5" /><ref name=":6" /> | |||
| ''Cloud architecture'',<ref></ref> the ] of the ] involved in the delivery of ''cloud computing'', typically involves multiple ''cloud components'' communicating with each other over ]s, usually ]s.<ref></ref> This resembles the ] of having multiple programs each doing one thing well and working together over universal interfaces. Complexity is controlled and the resulting systems are more manageable than their ] counterparts. | |||
| In practice, many organizations are increasingly adopting hybrid cloud architectures, combining on-premises infrastructure with cloud services. This approach allows businesses to balance scalability, cost-effectiveness, and control, offering the benefits of both deployment models while mitigating their respective limitations.<ref name=":3" /><ref name=":4" /><ref name=":5" /><ref name=":6" /> | |||
| ==History== | |||
| The underlying concept of cloud computing dates back to ], when ] opined that "computation may someday be organized as a ]"; indeed it shares characteristics with ]s that date back to the 1960s. The actual term "cloud" borrows from ] in that telecommunications companies, who until the 1990s primarily offered dedicated point-to-point data circuits, began offering ] (VPN) services with comparable quality of service but at a much lower cost. By switching traffic to balance utilization as they saw fit they were able to utilise their overall network bandwidth more effectively. The cloud symbol was used to denote the demarcation point between that which was the responsibility of the provider from that of the user. Cloud computing extends this boundary to cover servers as well as the network infrastructure.<ref></ref> | |||
| == Challenges and limitations == | |||
| ] played a key role in the development of cloud computing by modernizing their ]s after the ], which, like most ], were using as little as 10% of their capacity at any one time just to leave room for occasional spikes. Having found that the new cloud architecture resulted in significant internal efficiency improvements whereby small, fast-moving "two-pizza teams" could add new features faster and easier, Amazon started providing access to their systems through ] on a ] basis in ].<ref name="amazon">.</ref> | |||
| {{Main|Cloud computing issues}} | |||
| One of the main challenges of cloud computing, in comparison to more traditional on-premises computing, is data security and privacy. Cloud users entrust their sensitive data to third-party providers, who may not have adequate measures to protect it from unauthorized access, breaches, or leaks. Cloud users also face compliance risks if they have to adhere to certain regulations or standards regarding data protection, such as ] or ].<ref name="ttarget">{{cite web|url=https://www.techtarget.com/searchcloudcomputing/tip/Explore-the-pros-and-cons-of-cloud-computing|title=The pros and cons of cloud computing explained|last1=Marko|first1=Kurt|last2=Bigelow|first2=Stephen J.|date=10 Nov 2022|website=TechTarget}}</ref> | |||
| Another challenge of cloud computing is reduced visibility and control. Cloud users may not have full insight into how their cloud resources are managed, configured, or optimized by their providers. They may also have limited ability to customize or modify their cloud services according to their specific needs or preferences.<ref name="ttarget"/> Complete understanding of all technology may be impossible, especially given the scale, complexity, and deliberate opacity of contemporary systems; however, there is a need for understanding complex technologies and their interconnections to have power and agency within them.<ref>{{Cite book |last=Bratton |first=Benjamin H. |title=The stack: on software and sovereignty |date=2015 |publisher=MIT press |isbn=978-0-262-02957-5 |series=Software studies |location=Cambridge, Mass. London}}</ref> The ] of the cloud can be seen as problematic as cloud computing retains the aura of something ] and ]; it is something experienced without precisely understanding what it is or how it works.<ref>{{Cite book |last=Bridle |first=James |title=New dark age: technology and the end of the future |date=2019 |publisher=Verso |isbn= |edition= |location=}}</ref> | |||
| In ], ], ], and a number of universities embarked on a large scale cloud computing research project.<ref></ref> By mid-2008, Gartner saw an opportunity for cloud computing "to shape the relationship among consumers of IT services, those who use IT services and those who sell them",<ref>, Amy Schurr, Network World, 2008-07-08, citing the ] report, “Cloud Computing Confusion Leads to Opportunity”. Retrieved 2009-09-11.</ref> and observed that "rganisations are switching from company-owned hardware and software assets to per-use service-based models" so that the "projected shift to cloud computing ... will result in dramatic growth in IT products in some areas and significant reductions in other areas."<ref>, ], 2008-08-18. Retrieved 2009-09-11.</ref> | |||
| Additionally, cloud migration is a significant challenge. This process involves transferring data, applications, or workloads from one cloud environment to another, or from on-premises infrastructure to the cloud. Cloud migration can be complicated, time-consuming, and expensive, particularly when there are compatibility issues between different cloud platforms or architectures. If not carefully planned and executed, cloud migration can lead to downtime, reduced performance, or even data loss.<ref>{{cite web|url=https://www.forbes.com/sites/forbestechcouncil/2023/03/08/the-hidden-costs-of-cloud-migration|title=The Hidden Costs Of Cloud Migration|last=Shurma|first=Ramesh|date=8 Mar 2023|website=Forbes}}</ref> | |||
| == Key features == | |||
| <!-- Pros and Cons are discussed as 'key features' as each typically has both --> | |||
| <!-- Separate pros and cons lists are very confusing, with the same topics, e.g., security, listed in both --> | |||
| * ''']''' improves with users' ability to rapidly and inexpensively re-provision technological infrastructure resources.<ref></ref> | |||
| * ''']''' is claimed to be greatly reduced and ] is converted to ]<ref></ref>. This ostensibly lowers ], as infrastructure is typically provided by a third-party and does not need to be purchased for one-time or infrequent intensive computing tasks. Pricing on a ] basis is fine-grained with usage-based options and fewer IT skills are required for implementation (in-house).<ref name="idc"></ref> | |||
| * '''] and location independence'''<ref name="yarmis"></ref> enable users to access systems using a web browser regardless of their location or what device they are using (e.g., PC, mobile). As infrastructure is off-site (typically provided by a third-party) and accessed via the Internet, users can connect from anywhere.<ref name="idc" /> | |||
| * ''']''' enables sharing of resources and costs across a large pool of users thus allowing for: | |||
| ** '''Centralization''' of infrastructure in locations with lower costs (such as real estate, electricity, etc.) | |||
| ** '''Peak-load capacity''' increases (users need not engineer for highest possible load-levels) | |||
| ** '''Utilization and efficiency''' improvements for systems that are often only 10–20% utilized.<ref name="amazon"/> | |||
| * ''']''' improves through the use of multiple redundant sites, which makes cloud computing suitable for ] and ].<ref></ref> Nonetheless, many major cloud computing services have suffered outages, and IT and business managers can at times do little when they are affected.<ref></ref><ref name="cloudfeud"></ref> | |||
| * ''']''' via dynamic ("on-demand") ] of resources on a fine-grained, self-service basis near real-time, without users having to engineer for peak loads. ] is monitored, and consistent and loosely coupled architectures are constructed using ] as the system interface.<ref name="idc" /> One of the most important new methods for overcoming performance bottlenecks for a large class of applications is data parallel programming on a distributed data grid.<ref name="nubifer"></ref> | |||
| * ''' ]''' cloud computing resources usage should be measurable and should be metered per client and application on daily, weekly, monthly, and annual basis. This enables clients to choose the vendor cloud basing on cost and reliability. For vendors it enables ]. | |||
| === Cloud migration challenges === | |||
| ==Layers== | |||
| According to the 2024 State of the Cloud Report by ], approximately 50% of respondents identified the following top challenges when migrating workloads to ]:<ref name=":2">{{Cite journal |title=2024 State of the Cloud Report |url=https://info.flexera.com/CM-REPORT-State-of-the-Cloud-2024-Thanks |journal=Flexera's State of the Cloud Report}}</ref> | |||
| # "Understanding application dependencies" | |||
| ===Application=== | |||
| # "Comparing on-premise and cloud costs" | |||
| {{see also|Category:Cloud applications}} | |||
| # "Assessing technical feasibility." | |||
| === Implementation challenges === | |||
| Cloud application services or "''] (SaaS)''" deliver ] as a service over the ], eliminating the need to install and run the application on the customer's own computers and simplifying maintenance and support. Key characteristics include:<ref></ref> | |||
| Applications hosted in the cloud are susceptible to the ], a series of misconceptions that can lead to significant issues in software development and deployment.<ref>{{Cite book |title=Fundamentals of Software Architecture: An Engineering Approach |date=2020 |publisher=O'Reilly Media |isbn=978-1492043454}}</ref> | |||
| * Network-based access to, and management of, commercially available (i.e., not custom) software | |||
| * Activities that are managed from central locations rather than at each customer's site, enabling customers to access applications remotely via the Web | |||
| * Application delivery that typically is closer to a one-to-many model (single instance, multi-tenant architecture) than to a one-to-one model, including architecture, pricing, partnering, and management characteristics | |||
| * Centralized feature updating, which obviates the need for downloadable patches and upgrades. | |||
| === |
=== Cloud cost overruns === | ||
| In a report by ], a survey of 200 IT leaders revealed that 69% experienced budget overruns in their organizations' cloud expenditures during 2023. Conversely, 31% of IT leaders whose organizations stayed within budget attributed their success to accurate forecasting and budgeting, proactive monitoring of spending, and effective optimization.<ref>{{Cite web |title=2024 Cloud Spending: IT Balances Costs with GenAI Innovation |url=https://www.gartner.com/peer-community/oneminuteinsights/omi-keeping-cloud-costs-check-it-leader-perspectives-rfz |access-date=Nov 16, 2024 |website=Gartner Peer Community}}</ref> | |||
| {{see also|Category:Cloud platforms}} | |||
| The 2024 Flexera State of Cloud Report identifies the top cloud challenges as managing cloud spend, followed by security concerns and lack of expertise. Public cloud expenditures exceeded budgeted amounts by an average of 15%. The report also reveals that cost savings is the top cloud initiative for 60% of respondents. Furthermore, 65% measure cloud progress through cost savings, while 42% prioritize shorter time-to-market, indicating that cloud's promise of accelerated deployment is often overshadowed by cost concerns.<ref name=":2" /> | |||
| Cloud platform services or "''Platform as a Service (PaaS)''" deliver a ] and/or ] as a service, often consuming ''cloud infrastructure'' and sustaining ''cloud applications''.<ref></ref> It facilitates deployment of applications without the cost and complexity of buying and managing the underlying hardware and software layers.<ref></ref><ref></ref> | |||
| === Service Level Agreements === | |||
| ===Infrastructure=== | |||
| Typically, cloud providers' ] (SLAs) do not encompass all forms of service interruptions. Exclusions typically include planned maintenance, downtime resulting from external factors such as network issues, ]s, like misconfigurations, ]s, ] events, or ]. Typically, customers bear the responsibility of monitoring SLA compliance and must file claims for any unmet SLAs within a designated timeframe. Customers should be aware of how deviations from SLAs are calculated, as these parameters may vary by service. These requirements can place a considerable burden on customers. Additionally, SLA percentages and conditions can differ across various services within the same provider, with some services lacking any SLA altogether. In cases of service interruptions due to hardware failures in the cloud provider, the company typically does not offer monetary compensation. Instead, eligible users may receive credits as outlined in the corresponding SLA.<ref>{{Cite book |title=Cloud Security and Privacy An Enterprise Perspective on Risks and Compliance |date=4 September 2009 |publisher=O'Reilly Media |isbn=9781449379513}}</ref><ref>{{Cite book |title=Requirements Engineering for Service and Cloud Computing |date=10 April 2017 |publisher=Springer International Publishing |isbn=9783319513102}}</ref><ref>{{Cite book |last=Srinivasan |title=Cloud Computing Basics |date=14 May 2014 |publisher=Springer |isbn=9781461476993}}</ref><ref>{{Cite book |last=Murugesan |first=San |title=Encyclopedia of Cloud Computing |date=August 2016 |publisher=John Wiley & Sons |isbn=9781118821978}}</ref> | |||
| {{see also|Category:Cloud infrastructure}} | |||
| === Leaky abstractions === | |||
| Cloud infrastructure services or "''Infrastructure as a Service (IaaS)''" delivers ] ], typically a ] environment as a service. Rather than purchasing servers, software, data center space or network equipment, clients instead buy those resources as a fully outsourced service. The service is typically billed on a ] basis and amount of resources consumed (and therefore the cost) will typically reflect the level of activity. It is an evolution of ] offerings.<ref></ref> | |||
| Cloud computing ] aim to simplify resource management, but ]s can expose underlying complexities. These variations in abstraction quality depend on the cloud vendor, service and ]. Mitigating leaky abstractions requires users to understand the implementation details and limitations of the cloud services they utilize.<ref>{{Cite book |title=Cloud Native Infrastructure: Patterns for Scalable Infrastructure and Applications in a Dynamic Environment |date=25 October 2017 |publisher=O'Reilly Media |isbn=9781491984253}}</ref><ref>{{Cite book |title=Cloud Observability in Action |isbn=9781633439597 |last1=Hausenblas |first1=Michael |date=26 December 2023 |publisher=Simon and Schuster }}</ref><ref>{{Cite book |title=Microservices From Day One: Build robust and scalable software from the start |isbn=9781484219379 |last1=Jr |first1=Cloves Carneiro |last2=Schmelmer |first2=Tim |date=10 December 2016 |publisher=Apress }}</ref> | |||
| === Service lock-in within the same vendor === | |||
| == Deployment models == | |||
| Service lock-in within the same vendor occurs when a customer becomes dependent on specific services within a cloud vendor, making it challenging to switch to alternative services within the same vendor when their needs change.<ref>{{Cite book |title=Cloud Computing with the Windows Azure Platform |isbn=9781118058756 |last1=Jennings |first1=Roger |date=29 December 2010 |publisher=John Wiley & Sons }}</ref><ref>{{Cite book |title=Cloud and Virtual Data Storage Networking |isbn=9781466508446}}</ref> | |||
| ===Security and privacy=== | |||
| ] | |||
| {{Main|Cloud computing security}} | |||
| Cloud computing poses privacy concerns because the service provider can access the data that is in the cloud at any time. It could accidentally or deliberately alter or delete information.<ref name="ryan">{{cite web|url=https://cacm.acm.org/magazines/2011/1/103200-cloud-computing-privacy-concerns-on-our-doorstep/fulltext|title=Cloud Computing Privacy Concerns on Our Doorstep|first=Mark D.|last=Ryan|website=cacm.acm.org|date=January 2011 |access-date=2021-05-21|archive-date=2021-12-28|archive-url=https://web.archive.org/web/20211228121443/https://cacm.acm.org/magazines/2011/1/103200-cloud-computing-privacy-concerns-on-our-doorstep/fulltext|url-status=live}}</ref> Many cloud providers can share information with third parties if necessary for purposes of law and order without a warrant. That is permitted in their privacy policies, which users must agree to before they start using cloud services. Solutions to privacy include policy and legislation as well as end-users' choices for how data is stored.<ref name="ryan"/> Users can encrypt data that is processed or stored within the cloud to prevent unauthorized access.<ref name="ryan"/> ] can also provide practical solutions to privacy concerns in cloud computing. These systems distinguish between authorized and unauthorized users and determine the amount of data that is accessible to each entity.<ref>{{Cite journal|title=Identity and access management in cloud environment: Mechanisms and challenges|date=August 1, 2018|journal=Engineering Science and Technology|volume=21|issue=4|pages=574–588|doi=10.1016/j.jestch.2018.05.010|last1=Indu|first1=I.|last2=Anand|first2=P.M. Rubesh|last3=Bhaskar|first3=Vidhyacharan|doi-access=free}}</ref> The systems work by creating and describing identities, recording activities, and getting rid of unused identities. | |||
| According to the Cloud Security Alliance, the top three threats in the cloud are ''Insecure Interfaces and APIs'', ''Data Loss & Leakage'', and ''Hardware Failure''—which accounted for 29%, 25% and 10% of all cloud security outages respectively. Together, these form shared technology vulnerabilities. In a cloud provider platform being shared by different users, there may be a possibility that information belonging to different customers resides on the same data server. Additionally, ], chief technology officer at Emagined Security, said that hackers are spending substantial time and effort looking for ways to penetrate the cloud. "There are some real Achilles' heels in the cloud infrastructure that are making big holes for the bad guys to get into". Because data from hundreds or thousands of companies can be stored on large cloud servers, hackers can theoretically gain control of huge stores of information through a single attack—a process he called "hyperjacking". Some examples of this include the Dropbox security breach, and iCloud 2014 leak.<ref name="psg.hitachi-solutions.com">{{cite web|title = Google Drive, Dropbox, Box and iCloud Reach the Top 5 Cloud Storage Security Breaches List|url = https://psg.hitachi-solutions.com/credeon/blog/google-drive-dropbox-box-and-icloud-reach-the-top-5-cloud-storage-security-breaches-list|website = psg.hitachi-solutions.com|access-date = 2015-11-22|archive-url = https://web.archive.org/web/20151123032912/https://psg.hitachi-solutions.com/credeon/blog/google-drive-dropbox-box-and-icloud-reach-the-top-5-cloud-storage-security-breaches-list|archive-date = 2015-11-23|url-status=dead}}</ref> Dropbox had been breached in October 2014, having over seven million of its users passwords stolen by hackers in an effort to get monetary value from it by Bitcoins (BTC). By having these passwords, they are able to read ] as well as have this data be indexed by search engines (making the information public).<ref name="psg.hitachi-solutions.com"/> | |||
| There is the problem of legal ownership of the data (If a user stores some data in the cloud, can the cloud provider profit from it?). Many Terms of Service agreements are silent on the question of ownership.<ref>{{cite news |url=https://www.latimes.com/business/la-xpm-2012-apr-26-la-fi-tech-savvy-cloud-services-20120426-story.html |title=Who owns your stuff in the cloud? |date=26 April 2012 |first=Michelle |last=Maltais |newspaper=Los Angeles Times |access-date=2012-12-14 |archive-date=2013-01-20 |archive-url=https://web.archive.org/web/20130120124852/http://articles.latimes.com/2012/apr/26/business/la-fi-tech-savvy-cloud-services-20120426 |url-status=live }}</ref> Physical control of the computer equipment (private cloud) is more secure than having the equipment off-site and under someone else's control (public cloud). This delivers great incentive to public cloud computing service providers to prioritize building and maintaining strong management of secure services.<ref>{{cite web|url=https://www.networkworld.com/article/772953/virtualization-security-of-virtualization-cloud-computing-divides-it-and-security-pros.html|title=Security of virtualization, cloud computing divides IT and security pros|date=2010-02-22|publisher=Network World|access-date=2010-08-22|archive-date=2024-04-26|archive-url=https://web.archive.org/web/20240426183953/https://www.networkworld.com/article/772953/virtualization-security-of-virtualization-cloud-computing-divides-it-and-security-pros.html|url-status=live}}</ref> Some small businesses that do not have expertise in ] security could find that it is more secure for them to use a public cloud. There is the risk that end users do not understand the issues involved when signing on to a cloud service (persons sometimes do not read the many pages of the terms of service agreement, and just click "Accept" without reading). This is important now that cloud computing is common and required for some services to work, for example for an ] (Apple's ] or ]). Fundamentally, private cloud is seen as more secure with higher levels of control for the owner, however public cloud is seen to be more flexible and requires less time and money investment from the user.<ref>{{cite web | title=The Bumpy Road to Private Clouds | url=http://www.computerworld.com/article/2549867/data-center/the-bumpy-road-to-private-clouds.html | access-date=8 October 2014 | date=2010-12-20 | archive-date=2014-10-15 | archive-url=https://web.archive.org/web/20141015113110/http://www.computerworld.com/article/2549867/data-center/the-bumpy-road-to-private-clouds.html | url-status=live }}</ref> | |||
| The attacks that can be made on cloud computing systems include ] attacks, ] attacks, authentication attacks, and ] attacks. One of the largest threats is considered to be malware attacks, such as ]. Recent research conducted in 2022 has revealed that the Trojan horse injection method is a serious problem with harmful impacts on cloud computing systems.<ref>{{Cite journal |last1=Kanaker |first1=Hasan |last2=Karim |first2=Nader Abdel |last3=Awwad |first3=Samer A. B. |last4=Ismail |first4=Nurul H. A. |last5=Zraqou |first5=Jamal |last6=Ali |first6=Abdulla M. F. Al |date=2022-12-20 |title=Trojan Horse Infection Detection in Cloud Based Environment Using Machine Learning |url=https://online-journals.org/index.php/i-jim/article/view/35763 |journal=International Journal of Interactive Mobile Technologies |language=en |volume=16 |issue=24 |pages=81–106 |doi=10.3991/ijim.v16i24.35763 |s2cid=254960874 |issn=1865-7923|doi-access=free }}</ref> | |||
| ==Service models== | |||
| ] | |||
| ] | |||
| The ] recognized three cloud service models in 2011: ] (IaaS), ] (PaaS), and ] (SaaS).<ref name="nist" /> The International Organization for Standardization (ISO) later identified additional models in 2023, including ], "Communications as a Service", "Compute as a Service", and "].<ref name=":1">{{Cite journal |date=September 2023 |title=ISO/IEC 22123-2:2023(E) - Information technology — Cloud computing — Part 2: Concepts |journal=International Organization for Standardization}}</ref> | |||
| ===Infrastructure as a service (IaaS)=== | |||
| {{Main|Infrastructure as a service}} | |||
| Infrastructure as a service (IaaS) refers to online services that provide high-level ]s used to ] various low-level details of underlying network infrastructure like physical computing resources, location, data partitioning, scaling, security, backup, etc. A ] runs the virtual machines as guests. Pools of hypervisors within the cloud operational system can support large numbers of ]s and the ability to scale services up and down according to customers' varying requirements. Linux ] run in isolated partitions of a single ] running directly on the physical hardware. Linux ] and ]s are the underlying Linux kernel technologies used to isolate, secure and manage the containers. The use of containers offers higher performance than virtualization because there is no hypervisor overhead. IaaS clouds often offer additional resources such as a virtual-machine ] library, raw ], file or ], firewalls, ], ]es, ] (VLANs), and software bundles.<ref name="DHAC">{{cite book | |||
| |title = Developing and Hosting Applications on the Cloud | |||
| |date = July 2012 | |||
| |publisher = IBM Press | |||
| |isbn = 978-0-13-306684-5 | |||
| |chapter-url = http://www.ibmpressbooks.com/bookstore/product.asp?isbn=9780133066845 | |||
| |chapter = Infrastructure as a Service Cloud Concepts | |||
| |first1 = Alex | |||
| |last1 = Amies | |||
| |first2 = Harm | |||
| |last2 = Sluiman | |||
| |first3 = Qiang Guo | |||
| |last3 = Tong | |||
| |first4 = Guo Ning | |||
| |last4 = Liu | |||
| |access-date = 2012-07-19 | |||
| |archive-date = 2012-09-15 | |||
| |archive-url = https://web.archive.org/web/20120915124741/http://www.ibmpressbooks.com/bookstore/product.asp?isbn=9780133066845 | |||
| |url-status = dead | |||
| }}</ref> | |||
| {{Further|CloudBioLinux}} | |||
| The ]'s definition of cloud computing describes IaaS as "where the consumer is able to deploy and run arbitrary software, which can include operating systems and applications. The consumer does not manage or control the underlying cloud infrastructure but has control over operating systems, storage, and deployed applications; and possibly limited control of select networking components (e.g., host firewalls)."<ref name="nist"/> | |||
| IaaS-cloud providers supply these resources on-demand from their large pools of equipment installed in ]. For ] connectivity, customers can use either the Internet or ]s (dedicated ]s). To deploy their applications, cloud users install operating-system images and their application software on the cloud infrastructure. In this model, the cloud user patches and maintains the operating systems and the application software. Cloud providers typically bill IaaS services on a utility computing basis: cost reflects the number of resources allocated and consumed.<ref>{{cite journal |title=The Cloud, the Crowd, and Public Policy |jstor=43314918 |url=https://www.jstor.org/stable/43314918 |last1=Nelson |first1=Michael R. |journal=Issues in Science and Technology |year=2009 |volume=25 |issue=4 |pages=71–76 |access-date=2022-09-10 |archive-date=2022-09-10 |archive-url=https://web.archive.org/web/20220910171012/https://www.jstor.org/stable/43314918 |url-status=live }}</ref> | |||
| ===Platform as a service (PaaS)=== | |||
| {{Main|Platform as a service}} | |||
| The ]'s definition of cloud computing defines Platform as a Service as:<ref name="nist"/> | |||
| {{blockquote|text=The capability provided to the consumer is to deploy onto the cloud infrastructure consumer-created or acquired applications created using programming languages, libraries, services, and tools supported by the provider. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, or storage, but has control over the deployed applications and possibly configuration settings for the application-hosting environment.}} | |||
| PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a ], typically including an operating system, programming-language execution environment, database, and the web server. Application developers develop and run their software on a cloud platform instead of directly buying and managing the underlying hardware and software layers. With some PaaS, the underlying computer and storage resources scale automatically to match application demand so that the cloud user does not have to allocate resources manually.<ref>{{cite conference |author= Boniface, M. |title= Platform-as-a-Service Architecture for Real-Time Quality of Service Management in Clouds |conference= 5th International Conference on Internet and Web Applications and Services (ICIW) |year= 2010 |pages= 155–160 |place= Barcelona, Spain |publisher= IEEE |doi= 10.1109/ICIW.2010.91 |display-authors=etal}}</ref>{{request quotation|date=July 2015}} | |||
| Some integration and data management providers also use specialized applications of PaaS as delivery models for data. Examples include '''iPaaS (Integration Platform as a Service)''' and '''dPaaS (Data Platform as a Service)'''. iPaaS enables customers to develop, execute and govern integration flows.<ref name="GartnerGlossary">{{cite web|publisher= Gartner|work= Gartner IT Glossary|url= http://www.gartner.com/it-glossary/information-platform-as-a-service-ipaas|title= Integration Platform as a Service (iPaaS)|access-date= 2015-07-20|archive-date= 2015-07-29|archive-url= https://web.archive.org/web/20150729050824/http://www.gartner.com/it-glossary/information-platform-as-a-service-ipaas|url-status= live}}</ref> Under the iPaaS integration model, customers drive the development and deployment of integrations without installing or managing any hardware or middleware.<ref name="GartnerReferenceModel">{{cite web|last= Gartner|title= Gartner Reference Model for Integration PaaS|url= http://www.gartner.com/id=1729256|access-date= 16 January 2013|author2= Massimo Pezzini|author3= Paolo Malinverno|author4= Eric Thoo|archive-date= 1 July 2013|archive-url= https://web.archive.org/web/20130701033411/http://www.gartner.com/id=1729256|url-status= live}}</ref> dPaaS delivers integration—and data-management—products as a fully managed service.<ref name="ITBusinessEdge">{{cite web|title= IT Business Edge|url= http://www.itbusinessedge.com/blogs/integration/liaisons-data-platform-as-a-service-includes-data-mapping.html|author= Loraine Lawson|date= 3 April 2015|access-date= 6 July 2015|archive-date= 7 July 2015|archive-url= https://web.archive.org/web/20150707171204/http://www.itbusinessedge.com/blogs/integration/liaisons-data-platform-as-a-service-includes-data-mapping.html|url-status= live}}</ref> Under the dPaaS model, the PaaS provider, not the customer, manages the development and execution of programs by building data applications for the customer. dPaaS users access data through ] tools.<ref name="EnterpriseCIOForum">{{cite web|last= Enterprise CIO Forum|title= The Value of Data Platform-as-a-Service (dPaaS)|url= http://www.enterprisecioforum.com/en/blogs/gabriellowy/value-data-platform-service-dpaas|archive-url= https://web.archive.org/web/20150419045605/http://www.enterprisecioforum.com/en/blogs/gabriellowy/value-data-platform-service-dpaas|url-status=dead|archive-date= 19 April 2015|author2= Gabriel Lowy|access-date= 6 July 2015}}</ref> | |||
| ===Software as a service (SaaS)=== | |||
| {{Main|Software as a service}} | |||
| The ]'s definition of cloud computing defines Software as a Service as:<ref name="nist"/> | |||
| {{Blockquote|text= | |||
| The capability provided to the consumer is to use the provider's applications running on a ]. The applications are accessible from various client devices through either a thin client interface, such as a web browser (e.g., web-based email), or a program interface. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, storage, or even individual application capabilities, with the possible exception of limited user-specific application configuration settings.}} | |||
| In the software as a service (SaaS) model, users gain access to application software and ]. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee.<ref>{{cite encyclopedia|title=Definition of: SaaS|url=https://www.pcmag.com/encyclopedia/term/56112/saas|encyclopedia=PC Magazine Encyclopedia|publisher=]|access-date=14 May 2014|archive-date=14 July 2014|archive-url=https://web.archive.org/web/20140714175059/http://www.pcmag.com/encyclopedia/term/56112/saas|url-status=live}}</ref> In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability—which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand.<ref name="hamdaqa">{{cite book | |||
| |title = A Reference Model for Developing Cloud Applications | |||
| |first = Mohammad | |||
| |last = Hamdaqa | |||
| |url = http://www.stargroup.uwaterloo.ca/~mhamdaqa/publications/A%20REFERENCEMODELFORDEVELOPINGCLOUD%20APPLICATIONS.pdf | |||
| |access-date = 2012-05-23 | |||
| |archive-date = 2012-10-05 | |||
| |archive-url = https://web.archive.org/web/20121005002903/http://www.stargroup.uwaterloo.ca/~mhamdaqa/publications/A%20REFERENCEMODELFORDEVELOPINGCLOUD%20APPLICATIONS.pdf | |||
| |url-status = live | |||
| }}</ref> ]s distribute the work over the set of virtual machines. This process is transparent to the cloud user, who sees only a single access-point. To accommodate a large number of cloud users, cloud applications can be '']'', meaning that any machine may serve more than one cloud-user organization. | |||
| The pricing model for SaaS applications is typically a monthly or yearly flat fee per user,<ref name="Chou">{{cite book | |||
| |title = Introduction to Cloud Computing: Business & Technology | |||
| |first = Timothy | |||
| |last = Chou | |||
| |url = https://www.scribd.com/doc/64699897/Introduction-to-Cloud-Computing-Business-and-Technology | |||
| |access-date = 2017-09-09 | |||
| |archive-date = 2016-05-05 | |||
| |archive-url = https://web.archive.org/web/20160505045711/https://www.scribd.com/doc/64699897/Introduction-to-Cloud-Computing-Business-and-Technology | |||
| |url-status = live | |||
| }}</ref> so prices become scalable and adjustable if users are added or removed at any point. It may also be free.<ref>{{cite web|title=HVD: the cloud's silver lining |url=http://www.intrinsictechnology.co.uk/FileUploads/HVD_Whitepaper.pdf |archive-url=https://web.archive.org/web/20121002231021/http://www.intrinsictechnology.co.uk/FileUploads/HVD_Whitepaper.pdf |url-status=dead |archive-date=2 October 2012 |publisher=Intrinsic Technology |access-date=30 August 2012 }}</ref> Proponents claim that SaaS gives a ] the potential to reduce IT operational costs by ] hardware and software maintenance and support to the cloud provider. This enables the business to reallocate IT operations costs away from hardware/software spending and from personnel expenses, towards meeting other goals. In addition, with applications hosted centrally, updates can be released without the need for users to install new software. One drawback of ] comes with storing the users' data on the cloud provider's server. As a result,{{citation needed|date=July 2015}} there could be unauthorized access to the data.<ref>{{Cite journal|last1=Sun|first1=Yunchuan|last2=Zhang|first2=Junsheng|last3=Xiong|first3=Yongping|last4=Zhu|first4=Guangyu|date=2014-07-01|title=Data Security and Privacy in Cloud Computing|journal=International Journal of Distributed Sensor Networks|language=en|volume=10|issue=7|page=190903|doi=10.1155/2014/190903|s2cid=13213544|issn=1550-1477|doi-access=free}}</ref> Examples of applications offered as SaaS are ] and productivity software like Google Docs and Office Online. SaaS applications may be integrated with ] or ]s, which is the case with ] being integrated with ], and ] being integrated with ].<ref>{{Cite web |title=Use OneDrive with Office |url=https://support.microsoft.com/en-us/office/use-onedrive-with-office-b1c976de-ef52-4d53-950f-d48f2c6427df |access-date=2022-10-15 |website=Microsoft Support |archive-date=2022-10-15 |archive-url=https://web.archive.org/web/20221015223322/https://support.microsoft.com/en-us/office/use-onedrive-with-office-b1c976de-ef52-4d53-950f-d48f2c6427df |url-status=live }}</ref> | |||
| ===Serverless computing=== | |||
| {{Main|Serverless computing}} | |||
| Serverless computing allows customers to use various cloud capabilities without the need to provision, deploy, or manage hardware or software resources, apart from providing their application code or data. ISO/IEC 22123-2:2023 classifies serverless alongside Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) under the broader category of cloud service categories. Notably, while ISO refers to these classifications as cloud service categories, the National Institute of Standards and Technology (NIST) refers to them as service models.<ref name="nist" /><ref name=":1" /> | |||
| ==Deployment models== | |||
| <!-- TODO: find source & add community cloud --> | <!-- TODO: find source & add community cloud --> | ||
| ] | ] | ||
| "A cloud deployment model represents the way in which cloud computing can be organized based on the control and sharing of physical or virtual resources."<ref name=":1" /> Cloud deployment models define the fundamental patterns of interaction between cloud customers and cloud providers. They do not detail implementation specifics or the configuration of resources.<ref name=":1" /> | |||
| ''Public cloud'' or ''external cloud'' describes cloud computing in the traditional mainstream sense, whereby resources are dynamically provisioned on a fine-grained, self-service basis over the Internet, via ]s/]s, from an off-site third-party provider who ] and bills on a fine-grained ] basis.<ref name="idc"/> | |||
| === |
===Private{{anchor|Private cloud|Private Cloud}}=== | ||
| Private cloud is cloud infrastructure operated solely for a single organization, whether managed internally or by a third party, and hosted either internally or externally.<ref name="nist" /> Undertaking a private cloud project requires significant engagement to virtualize the business environment, and requires the organization to reevaluate decisions about existing resources. It can improve business, but every step in the project raises security issues that must be addressed to prevent serious vulnerabilities. Self-run ]s<ref>{{cite web |url=http://www.govconnection.com/IPA/PM/Info/Cloud-Computing/Self-Run-Private-Cloud.htm |title=Self-Run Private Cloud Computing Solution – GovConnection |work=govconnection.com |year=2014 |access-date=April 15, 2014 |archive-date=April 6, 2014 |archive-url=https://web.archive.org/web/20140406092811/http://www.govconnection.com/IPA/PM/Info/Cloud-Computing/Self-Run-Private-Cloud.htm |url-status=live }}</ref> are generally capital intensive. They have a significant physical footprint, requiring allocations of space, hardware, and environmental controls. These assets have to be refreshed periodically, resulting in additional capital expenditures. They have attracted criticism because users "still have to buy, build, and manage them" and thus do not benefit from less hands-on management,<ref name="iwpc">{{cite web|title=Private Clouds Take Shape – Services – Business services – Informationweek|url=http://www.informationweek.com/services/business/private-clouds-take-shape/209904474|date=2012-09-09|archive-url=https://archive.today/20120909095216/http://www.informationweek.com/services/business/private-clouds-take-shape/209904474|archive-date=2012-09-09}}</ref> essentially " the economic model that makes cloud computing such an intriguing concept".<ref>{{cite web |last=Haff |first=Gordon |url=https://www.cnet.com/news/just-dont-call-them-private-clouds/ |title=Just don't call them private clouds |publisher=CNET News |date=2009-01-27 |access-date=2010-08-22 |archive-date=2014-12-27 |archive-url=https://web.archive.org/web/20141227001927/http://www.cnet.com/news/just-dont-call-them-private-clouds/ |url-status=live }}</ref><ref>{{cite web|title=There's No Such Thing As A Private Cloud – Cloud-computing -|url=http://www.informationweek.com/cloud-computing/theres-no-such-thing-as-a-private-cloud/229207922|date=2013-01-26|archive-url=https://archive.today/20130126064248/http://www.informationweek.com/cloud-computing/theres-no-such-thing-as-a-private-cloud/229207922|archive-date=2013-01-26|url-status=dead}}</ref> | |||
| ===Public=== | |||
| A ''community cloud'' may be established where several organizations have similar requirements and seek to share infrastructure so as to realize some of the benefits of cloud computing. With the costs spread over fewer users than a ''public cloud'' (but more than a single tenant) this option is more expensive but may offer a higher level of privacy, security and/or policy compliance. Examples of ''community cloud'' include ]'s "Gov Cloud".<ref></ref><!-- any others? --> | |||
| {{self-reference|For a comparison of cloud-computing software and providers, see ]}} | |||
| Cloud services are considered "public" when they are delivered over the public Internet, and they may be offered as a paid subscription, or free of charge.<ref>{{cite web|first=Margaret|last=Rouse|title=What is public cloud?|access-date=12 October 2014|url=http://searchcloudcomputing.techtarget.com/definition/public-cloud|publisher=Definition from Whatis.com|archive-date=16 October 2014|archive-url=https://web.archive.org/web/20141016022343/http://searchcloudcomputing.techtarget.com/definition/public-cloud|url-status=live}}</ref> Architecturally, there are few differences between public- and private-cloud services, but security concerns increase substantially when services (applications, storage, and other resources) are shared by multiple customers. Most public-cloud providers offer direct-connection services that allow customers to securely link their legacy data centers to their cloud-resident applications.<ref name="idc">{{cite web |date=2008-09-23 |title=Defining 'Cloud Services' and "Cloud Computing" |url=http://blogs.idc.com/ie/?p=190 |url-status=dead |archive-url=https://web.archive.org/web/20100722074526/http://blogs.idc.com/ie/?p=190 |archive-date=2010-07-22 |access-date=2010-08-22 |publisher=IDC}}</ref><ref>{{cite web|url=https://cloud.oracle.com/en_US/fastconnect|title=FastConnect {{!}} Oracle Cloud Infrastructure|website=cloud.oracle.com|access-date=2017-11-15|archive-date=2017-11-15|archive-url=https://web.archive.org/web/20171115232022/https://cloud.oracle.com/en_US/fastconnect|url-status=live}}</ref> | |||
| Several factors like the functionality of the solutions, ], integrational and ]al aspects as well as ] are influencing the decision of enterprises and organizations to choose a public cloud or ] solution.<ref>{{Cite journal|last1=Schmidt|first1=Rainer|last2=Möhring|first2=Michael|last3=Keller|first3=Barbara|date=2017|title=Customer Relationship Management in a Public Cloud environment - Key influencing factors for European enterprises|journal=HICSS|series=Proceedings of the 50th Hawaii International Conference on System Sciences (2017)|doi=10.24251/HICSS.2017.513|hdl=10125/41673|isbn=9780998133102|doi-access=free|hdl-access=free}}</ref> | |||
| === Hybrid cloud === | |||
| A ''hybrid cloud'' environment consisting of multiple internal and/or external providers<ref></ref> "will be typical for most enterprises".<ref name="iwpc" /> By integrating multiple cloud services users may be able to ease the transition to ''public cloud'' services while avoiding issues such as ].<ref></ref><br /> | |||
| <br /> | |||
| Another perspective on deploying a web application in the cloud is using ], where the hosting infrastructure is a mix between ] for the web server, and ] for the database server. | |||
| === |
===Hybrid=== | ||
| {{see also|Hybrid cloud storage}} | |||
| ''Private cloud'' and ''internal cloud'' are ] that some vendors have recently used to describe offerings that emulate cloud computing on private networks. These (typically ] ]) products claim to "deliver some benefits of cloud computing without the pitfalls", capitalising on data security, corporate governance, and reliability concerns. They have been criticized on the basis that users "still have to buy, build, and manage them" and as such do not benefit from lower up-front capital costs and less hands-on management<ref name="iwpc"></ref>, essentially " the economic model that makes cloud computing such an intriguing concept".<ref></ref><ref></ref> | |||
| '''Hybrid''' cloud is a composition of a public cloud and a private environment, such as a private cloud or on-premises resources,<ref>{{cite web|url=https://searchcloudcomputing.techtarget.com/definition/hybrid-cloud|title=What is hybrid cloud? - Definition from WhatIs.com|website=SearchCloudComputing|language=en|access-date=2019-08-10|archive-date=2019-07-16|archive-url=https://web.archive.org/web/20190716045359/https://searchcloudcomputing.techtarget.com/definition/hybrid-cloud|url-status=live}}</ref><ref>{{cite web|url=https://www.networkworld.com/article/3233132/what-is-hybrid-cloud-computing.html|title=What is hybrid cloud computing? The benefits of mixing private and public cloud services|last=Butler|first=Brandon|date=2017-10-17|website=Network World|language=en|access-date=2019-08-11|archive-date=2019-08-11|archive-url=https://web.archive.org/web/20190811183947/https://www.networkworld.com/article/3233132/what-is-hybrid-cloud-computing.html|url-status=live}}</ref> that remain distinct entities but are bound together, offering the benefits of multiple deployment models. Hybrid cloud can also mean the ability to connect collocation, managed and/or dedicated services with cloud resources.<ref name="nist" /> ] defines a hybrid cloud service as a cloud computing service that is composed of some combination of private, public and community cloud services, from different service providers.<ref>{{cite web|url=http://blogs.gartner.com/thomas_bittman/2012/09/24/mind-the-gap-here-comes-hybrid-cloud/|title=Mind the Gap: Here Comes Hybrid Cloud – Thomas Bittman|work=Thomas Bittman|date=24 September 2012|access-date=22 April 2015|archive-date=17 April 2015|archive-url=https://web.archive.org/web/20150417185305/http://blogs.gartner.com/thomas_bittman/2012/09/24/mind-the-gap-here-comes-hybrid-cloud/|url-status=live}}</ref> A hybrid cloud service crosses isolation and provider boundaries so that it cannot be simply put in one category of private, public, or community cloud service. It allows one to extend either the capacity or the capability of a cloud service, by aggregation, integration or customization with another cloud service. | |||
| Varied use cases for hybrid cloud composition exist. For example, an organization may store sensitive client data in house on a private cloud application, but interconnect that application to a business intelligence application provided on a public cloud as a software service.<ref>{{cite web |url=http://www.cio.com/article/753708/Business_Intelligence_Takes_to_Cloud_for_Small_Businesses |title=Business Intelligence Takes to Cloud for Small Businesses |publisher=CIO.com |date=2014-06-04 |access-date=2014-06-04 |archive-date=2014-06-07 |archive-url=https://web.archive.org/web/20140607002519/http://www.cio.com/article/753708/Business_Intelligence_Takes_to_Cloud_for_Small_Businesses |url-status=live }}</ref> This example of hybrid cloud extends the capabilities of the enterprise to deliver a specific business service through the addition of externally available public cloud services. Hybrid cloud adoption depends on a number of factors such as data security and compliance requirements, level of control needed over data, and the applications an organization uses.<ref>{{cite web|url=https://www.techradar.com/news/internet/cloud-services/hybrid-cloud-is-it-right-for-your-business-1261343|title=Hybrid cloud: is it right for your business?|author=Désiré Athow|work=TechRadar|date=24 August 2014|access-date=22 April 2015|archive-date=7 July 2017|archive-url=https://web.archive.org/web/20170707094750/http://www.techradar.com/news/internet/cloud-services/hybrid-cloud-is-it-right-for-your-business-1261343|url-status=live}}</ref> | |||
| == Issues == | |||
| === Privacy === | |||
| The Cloud model has been criticized by privacy advocates for the greater ease in which the companies hosting the Cloud services control, and thus, can monitor at will, lawfully or unlawfully, the communication and data stored between the user and the host company. Instances such as the secret ] program, working with ], and ], which recorded over 10 million phone calls between American citizens, causes uncertainty among privacy advocates, and the greater powers it gives to telecommunication companies to monitor user activity.<ref></ref> | |||
| While there have been efforts (such as ]) to "harmonise" the legal environment, providers such as ] still cater to major markets (typically the ] and the ]) by deploying local infrastructure and allowing customers to select "availability zones."<ref></ref> | |||
| Another example of hybrid cloud is one where ] organizations use public cloud computing resources to meet temporary capacity needs that can not be met by the private cloud.<ref>Metzler, Jim; Taylor, Steve. (2010-08-23) {{Webarchive|url=https://web.archive.org/web/20130619095824/http://www.networkworld.com/newsletters/frame/2010/082310wan1.html |date=2013-06-19 }}, Network World.</ref> This capability enables hybrid clouds to employ cloud bursting for scaling across clouds.<ref name="nist" /> ] is an application deployment model in which an application runs in a private cloud or data center and "bursts" to a public cloud when the demand for computing capacity increases. A primary advantage of cloud bursting and a hybrid cloud model is that an organization pays for extra compute resources only when they are needed.<ref>Rouse, Margaret. {{Webarchive|url=https://web.archive.org/web/20130319074247/http://searchcloudcomputing.techtarget.com/definition/cloud-bursting |date=2013-03-19 }}, May 2011. SearchCloudComputing.com.</ref> Cloud bursting enables data centers to create an in-house IT infrastructure that supports average workloads, and use cloud resources from public or private clouds, during spikes in processing demands.<ref>{{cite web|url=http://insights.dice.com/2012/06/21/how-cloudbursting-rightsizes-the-data-center/|title=How Cloudbursting "Rightsizes" the Data Center|date=2012-06-22|access-date=2016-10-19|archive-date=2016-10-19|archive-url=https://web.archive.org/web/20161019150709/http://insights.dice.com/2012/06/21/how-cloudbursting-rightsizes-the-data-center/|url-status=live}}</ref> | |||
| === Security === | |||
| {{main|Cloud computing security}} | |||
| === Community === | |||
| The relative security of cloud computing services is a contentious issue which may be delaying its adoption.<ref></ref> Some argue that customer data is more secure when managed internally, while others argue that cloud providers have a strong incentive to maintain trust and as such employ a higher level of security.<ref></ref> | |||
| ] shares infrastructure between several organizations from a specific community with common concerns (security, compliance, jurisdiction, etc.), whether it is managed internally or by a third-party, and hosted internally or externally, the costs are distributed among fewer users compared to a public cloud (but more than a private cloud). As a result, only a portion of the potential cost savings of cloud computing is achieved. | |||
| <ref name="nist" /> | |||
| === Multi cloud === | |||
| The Cloud Security Alliance is a non-profit organization formed to promote the use of best practices for providing security assurance within Cloud Computing.<ref></ref> | |||
| {{Main|Multicloud}} | |||
| According to ]/IEC 22123-1: "multi-cloud is a cloud deployment model in which a customer uses public cloud services provided by two or more cloud service providers". <ref>{{Cite journal |title=ISO/IEC 22123-1:2023(E) - Information technology — Cloud computing — Part 1: Vocabulary |journal=International Organization for Standardization |pages=2}}</ref> Poly cloud refers to the use of multiple public clouds for the purpose of leveraging specific services that each provider offers. It differs from Multi cloud in that it is not designed to increase flexibility or mitigate against failures but is rather used to allow an organization to achieve more than could be done with a single provider.<ref>{{cite web|url=https://hub.packtpub.com/polycloud-a-better-alternative-to-cloud-agnosticism/|title=Polycloud: a better alternative to cloud agnosticism|last=Gall|first=Richard|date=2018-05-16|website=Packt Hub|language=en-US|access-date=2019-11-11|archive-date=2019-11-11|archive-url=https://web.archive.org/web/20191111115325/https://hub.packtpub.com/polycloud-a-better-alternative-to-cloud-agnosticism/|url-status=live}}</ref> | |||
| === Compliance === | |||
| In order to obtain compliance with regulations including ], ] and ] in the ], the ] in the ] and the credit card industry's ], users may have to adopt ''community'' or ''hybrid'' deployment modes which are typically more expensive and may offer restricted benefits. This is how ] is able to "manage and meet additional government policy requirements beyond FISMA"<ref></ref><ref></ref> and ] are able to claim ] compliance.<ref></ref> Customers in the EU contracting with Cloud Providers established outside the EU/EEA have to adhere to the EU regulations on export of personal data<ref>http://www.thomashelbing.com/en/how-new-eu-rules-data-export-affect-companies-and-outside-eu</ref>. | |||
| ==Market== | |||
| Many providers also obtain ] certification (e.g. Amazon<ref></ref>, Google<ref></ref> and Microsoft<ref></ref>), but this has been criticised on the grounds that the hand-picked set of goals and standards determined by the auditor and the auditee are often not disclosed and can vary widely.<ref></ref> Providers typically make this information available on request, under ].<ref></ref> | |||
| According to ] (IDC), global spending on cloud computing services has reached $706 billion and is expected to reach $1.3 trillion by 2025.<ref>{{cite web |url=https://www.idc.com/getdoc.jsp?containerId=prUS48208321 |title=IDC Forecasts Worldwide "Whole Cloud" Spending to Reach $1.3 Trillion by 2025 |publisher=Idc.com |date=2021-09-14 |access-date=2022-07-30 |archive-date=2022-07-29 |archive-url=https://web.archive.org/web/20220729205418/https://www.idc.com/getdoc.jsp?containerId=prUS48208321 |url-status=live }}</ref> ] estimated that global public cloud services end-user spending would reach $600 billion by 2023.<ref>{{cite web | url=https://www.gartner.com/en/newsroom/press-releases/2022-04-19-gartner-forecasts-worldwide-public-cloud-end-user-spending-to-reach-nearly-500-billion-in-2022 | title=Gartner Forecasts Worldwide Public Cloud End-User Spending to Reach Nearly $500 Billion in 2022 | access-date=2022-07-25 | archive-date=2022-07-25 | archive-url=https://web.archive.org/web/20220725062816/https://www.gartner.com/en/newsroom/press-releases/2022-04-19-gartner-forecasts-worldwide-public-cloud-end-user-spending-to-reach-nearly-500-billion-in-2022 | url-status=live }}</ref> According to a ] report, cloud cost-optimization levers and value-oriented business use cases foresee more than $1 trillion in run-rate EBITDA across ] companies as up for grabs in 2030.<ref>{{cite web |url=https://www.mckinsey.com/business-functions/mckinsey-digital/our-insights/clouds-trillion-dollar-prize-is-up-for-grabs |title=Cloud's trillion-dollar prize is up for grabs |publisher=McKinsey |date= |access-date=2022-07-30 |archive-date=2022-07-25 |archive-url=https://web.archive.org/web/20220725062821/https://www.mckinsey.com/business-functions/mckinsey-digital/our-insights/clouds-trillion-dollar-prize-is-up-for-grabs |url-status=live }}</ref> In 2022, more than $1.3 trillion in enterprise IT spending was at stake from the shift to the cloud, growing to almost $1.8 trillion in 2025, according to Gartner.<ref>{{cite web | url=https://www.gartner.com/en/newsroom/press-releases/2022-02-09-gartner-says-more-than-half-of-enterprise-it-spending | title=Gartner Says More Than Half of Enterprise IT Spending in Key Market Segments Will Shift to the Cloud by 2025 | access-date=2022-07-25 | archive-date=2022-07-25 | archive-url=https://web.archive.org/web/20220725062759/https://www.gartner.com/en/newsroom/press-releases/2022-02-09-gartner-says-more-than-half-of-enterprise-it-spending | url-status=live }}</ref> | |||
| The European Commission's 2012 ''Communication'' identified several issues which were impeding the development of the cloud computing market:<ref name="ec529">European Commission, , COM(2012) 529 final, page 3, published 27 September 2012, accessed 26 April 2024</ref>{{rp|Section 3}} | |||
| === Legal === | |||
| *fragmentation of the ] across the EU | |||
| In March 2007, ] applied to ] the term "cloud computing" ({{US trademark|77139082}}) in the ]. The "Notice of Allowance" the company received in July 2008 was cancelled in August, resulting in a formal rejection of the trademark application less than a week later. | |||
| *concerns about ]s including reservations about data access and ownership, ], and ] | |||
| *variations in standards applicable to cloud computing | |||
| The ''Communication'' set out a series of "digital agenda actions" which the Commission proposed to undertake in order to support the development of a fair and effective market for cloud computing services.<ref name=ec529 />{{rp|Pages 6–14}} | |||
| ==List of public clouds== | |||
| Since 2007, the number of trademark filings covering cloud computing brands, goods and services has increased at an almost exponential rate. <ref> Inside Trademarks <http://insidetrademarks.com/2010/03/24/cloud-computing-trademark-trends/>, March 24, 2010 </ref> As companies sought to better position themselves for cloud computing branding and marketing efforts, cloud computing trademark filings increased by 483% between 2008 and 2009. <ref> Inside Trademarks <http://insidetrademarks.com/2010/03/24/cloud-computing-trademark-trends/>, March 24, 2010 </ref> In 2009, 116 cloud computing trademarks were filed, and trademark analysts predict that over 500 such marks could be filed during 2010. <ref> Inside Trademarks <http://insidetrademarks.com/2010/03/24/cloud-computing-trademark-trends/>, March 24, 2010 </ref> | |||
| * ] | |||
| === Open source === | |||
| * ] | |||
| ] are critical to the growth of cloud computing, and ] has provided the foundation for many cloud computing implementations.<ref></ref> In November 2007, the ] released the ], a version of ] intended to close a perceived ] associated with ] designed to be run over a network.<ref></ref> | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| ==Similar concepts== | |||
| === Open standards === | |||
| <!-- this need not enumerate every different type of computing, just the top half-dozen that are related to cloud computing --> | |||
| {{see also|Category:Cloud standards}} | |||
| The goal of cloud computing is to allow users to take benefit from all of these technologies, without the need for deep knowledge about or expertise with each one of them. The cloud aims to cut costs and helps the users focus on their core business instead of being impeded by IT obstacles.<ref name=HAM2012>{{cite book|last=HAMDAQA|first=Mohammad|title=Cloud Computing Uncovered: A Research Landscape|year=2012|publisher=Elsevier Press|isbn=978-0-12-396535-6|pages=41–85|url=http://www.stargroup.uwaterloo.ca/~mhamdaqa/publications/Cloud_Computing_Uncovered.pdf|access-date=2013-03-19|archive-date=2013-06-19|archive-url=https://web.archive.org/web/20130619150209/http://www.stargroup.uwaterloo.ca/~mhamdaqa/publications/Cloud_Computing_Uncovered.pdf|url-status=live}}</ref> The main enabling technology for cloud computing is ]. Virtualization software separates a physical computing device into one or more "virtual" devices, each of which can be easily used and managed to perform computing tasks. With ] essentially creating a scalable system of multiple independent computing devices, idle computing resources can be allocated and used more efficiently. Virtualization provides the agility required to speed up IT operations and reduces cost by increasing infrastructure ]. Autonomic computing automates the process through which the user can provision resources ]. By minimizing user involvement, automation speeds up the process, reduces labor costs and reduces the possibility of human errors.<ref name=HAM2012/> | |||
| Most cloud providers expose ] which are typically well-documented (often under a ] license<ref></ref>) however also unique to their implementation and thus not interoperable. Some vendors have adopted others' APIs<ref></ref> and there are a number of ]s under development, including the ]'s ]. The Open Cloud Consortium (OCC) <ref></ref> is working to develop consensus on early cloud computing standards and practices. | |||
| Cloud computing uses concepts from utility computing to provide ]s for the services used. Cloud computing attempts to address QoS (quality of service) and ] problems of other ] models.<ref name=HAM2012/> | |||
| === Sustainability === | |||
| Although cloud computing is often assumed to be a form of "]", there is as of yet no published study to substantiate this assumption. | |||
| <ref>{{cite news | |||
| | author = James Urquhart | |||
| | title = Cloud computing's green paradox | |||
| | quote = ...there is some significant evidence that the cloud is encouraging more compute consumption | |||
| | publisher = ''CNET News'' | |||
| | date = January 7, 2010 | |||
| | pages = | |||
| | url = http://news.cnet.com/8301-19413_3-10428065-240.html | |||
| | accessdate = March 12, 2010 | |||
| }}</ref> | |||
| Cloud computing shares characteristics with: | |||
| * ] {{En dash}} ''Client–server computing'' refers broadly to any ] that distinguishes between service providers (servers) and service requestors (clients).<ref>{{cite web|url=http://java.sun.com/developer/Books/jdbc/ch07.pdf|publisher=Sun Microsystem|title=Distributed Application Architecture|access-date=2009-06-16|archive-date=2011-04-06|archive-url=https://web.archive.org/web/20110406121920/http://java.sun.com/developer/Books/jdbc/ch07.pdf|url-status=live}}</ref> | |||
| * ] {{En dash}} A ] providing computer services, particularly from the 1960s to 1980s. | |||
| * ] {{En dash}} A form of distributed and parallel computing, whereby a 'super and virtual computer' is composed of a ] of networked, ] computers acting in concert to perform very large tasks. | |||
| * ] {{En dash}} Distributed computing paradigm that provides data, compute, storage and application services closer to the client or near-user edge devices, such as network routers. Furthermore, fog computing handles data at the network level, on smart devices and on the end-user client-side (e.g. mobile devices), instead of sending data to a remote location for processing. | |||
| * ] {{En dash}} The "packaging of ], such as computation and storage, as a metered service similar to a traditional public utility, such as electricity."<ref name="It's you've">{{cite journal|title=A break in the clouds: Towards a cloud definition|journal= ACM SIGCOMM Computer Communication Review|volume=39 |issue=1 |pages=50–55 |doi=10.1145/1496091.1496100 |date=December 2008 |last1=Vaquero |first1=Luis M. |last2=Rodero-Merino |first2=Luis |last3=Caceres |first3=Juan |last4=Lindner |first4=Maik |s2cid=207171174 |doi-access=free }}</ref><ref>{{cite web |last=Danielson |first=Krissi |url=http://www.ebizq.net/blogs/saasweek/2008/03/distinguishing_cloud_computing/ |title=Distinguishing Cloud Computing from Utility Computing |publisher=Ebizq.net |date=2008-03-26 |access-date=2010-08-22 |archive-date=2017-11-10 |archive-url=https://web.archive.org/web/20171110162550/http://www.ebizq.net/blogs/saasweek/2008/03/distinguishing_cloud_computing/ |url-status=live }}</ref> | |||
| * ] {{En dash}} A distributed architecture without the need for central coordination. Participants are both suppliers and consumers of resources (in contrast to the traditional client-server model). | |||
| *] {{En dash}} A live, isolated computer environment in which a program, code or file can run without affecting the application in which it runs. | |||
| ==See also== | |||
| <!---♦♦♦ Please keep the list in alphabetical order ♦♦♦---> | |||
| {{div col|colwidth=20em}} | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| ** ] | |||
| ** ] | |||
| ** ] | |||
| * ] | |||
| * ] | |||
| * ] (] computing) | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| * ] | |||
| {{Div col end}} | |||
| ==Notes== | |||
| {{notelist}} | |||
| ==References== | ==References== | ||
| {{reflist |
{{reflist}} | ||
| ==Further reading== | |||
| * {{cite book|last1=Millard|first1=Christopher|title=Cloud Computing Law|date=2013|publisher=Oxford University Press|isbn=978-0-19-967168-7|url=https://global.oup.com/academic/product/cloud-computing-law-9780198716662?cc=gb&lang=en&}} | |||
| * Weisser, Alexander (2020). . Editions Juridiques Libres, {{ISBN|978-2-88954-030-3}}. | |||
| * {{cite journal|last1=Singh|first1=Jatinder|last2=Powles|first2=Julia|last3=Pasquier|first3=Thomas|last4=Bacon|first4=Jean|s2cid=9812531|title=Data Flow Management and Compliance in Cloud Computing|journal=IEEE Cloud Computing|date=July 2015|volume=2|issue=4|pages=24–32|doi=10.1109/MCC.2015.69|url=https://www.repository.cam.ac.uk/handle/1810/255049}} | |||
| * {{cite journal|last1=Armbrust|first1=Michael|last2=Stoica|first2=Ion|last3=Zaharia|first3=Matei|last4=Fox|first4=Armando|last5=Griffith|first5=Rean|last6=Joseph|first6=Anthony D.|last7=Katz|first7=Randy|last8=Konwinski|first8=Andy|last9=Lee|first9=Gunho|last10=Patterson|first10=David|last11=Rabkin|first11=Ariel|s2cid=1673644|title=A view of cloud computing|journal=Communications of the ACM|date=1 April 2010|volume=53|issue=4|page=50|doi=10.1145/1721654.1721672|doi-access=free}} | |||
| * {{cite book|last1=Hu|first1=Tung-Hui|title=A Prehistory of the Cloud|date=2015|publisher=MIT Press|isbn=978-0-262-02951-3}} | |||
| * Mell, P. (2011, September). ''''. Retrieved November 1, 2015, from National Institute of Standards and Technology website | |||
| {{Commons category-inline}} | |||
| {{Wikiquote}} | |||
| {{Cloud computing}} | {{Cloud computing}} | ||
| {{Parallel computing}} | |||
| {{Authority control}} | |||
| {{DEFAULTSORT:Cloud Computing}} | {{DEFAULTSORT:Cloud Computing}} | ||
| ] | ] | ||
| ] | ] | ||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
| ] | |||
Latest revision as of 01:35, 8 January 2025
Form of shared internet-based computing "Cloud Computing" redirects here. Not to be confused with Cloud Computing (horse).

"Cloud computing is a paradigm for enabling network access to a scalable and elastic pool of shareable physical or virtual resources with self-service provisioning and administration on-demand," according to ISO.
Essential Characteristics
In 2011, the National Institute of Standards and Technology (NIST) identified five "essential characteristics" for cloud systems. Below are the exact definitions according to NIST:
- On-demand self-service: "A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service provider."
- Broad network access: "Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, tablets, laptops, and workstations)."
- Resource pooling: " The provider's computing resources are pooled to serve multiple consumers using a multi-tenant model, with different physical and virtual resources dynamically assigned and reassigned according to consumer demand."
- Rapid elasticity: "Capabilities can be elastically provisioned and released, in some cases automatically, to scale rapidly outward and inward commensurate with demand. To the consumer, the capabilities available for provisioning often appear unlimited and can be appropriated in any quantity at any time."
- Measured service: "Cloud systems automatically control and optimize resource use by leveraging a metering capability at some level of abstraction appropriate to the type of service (e.g., storage, processing, bandwidth, and active user accounts). Resource usage can be monitored, controlled, and reported, providing transparency for both the provider and consumer of the utilized service.
By 2023, the International Organization for Standardization (ISO) had expanded and refined the list.
History
Main article: History of cloud computingThe history of cloud computing extends back to the 1960s, with the initial concepts of time-sharing becoming popularized via remote job entry (RJE). The "data center" model, where users submitted jobs to operators to run on mainframes, was predominantly used during this era. This was a time of exploration and experimentation with ways to make large-scale computing power available to more users through time-sharing, optimizing the infrastructure, platform, and applications, and increasing efficiency for end users.
The "cloud" metaphor for virtualized services dates to 1994, when it was used by General Magic for the universe of "places" that mobile agents in the Telescript environment could "go". The metaphor is credited to David Hoffman, a General Magic communications specialist, based on its long-standing use in networking and telecom. The expression cloud computing became more widely known in 1996 when Compaq Computer Corporation drew up a business plan for future computing and the Internet. The company's ambition was to supercharge sales with "cloud computing-enabled applications". The business plan foresaw that online consumer file storage would likely be commercially successful. As a result, Compaq decided to sell server hardware to internet service providers.
In the 2000s, the application of cloud computing began to take shape with the establishment of Amazon Web Services (AWS) in 2002, which allowed developers to build applications independently. In 2006 Amazon Simple Storage Service, known as Amazon S3, and the Amazon Elastic Compute Cloud (EC2) were released. In 2008 NASA's development of the first open-source software for deploying private and hybrid clouds.
The following decade saw the launch of various cloud services. In 2010, Microsoft launched Microsoft Azure, and Rackspace Hosting and NASA initiated an open-source cloud-software project, OpenStack. IBM introduced the IBM SmartCloud framework in 2011, and Oracle announced the Oracle Cloud in 2012. In December 2019, Amazon launched AWS Outposts, a service that extends AWS infrastructure, services, APIs, and tools to customer data centers, co-location spaces, or on-premises facilities.
Value proposition
Cloud computing can enable shorter time to market by providing pre-configured tools, scalable resources, and managed services, allowing users to focus on their core business value instead of maintaining infrastructure. Cloud platforms can enable organizations and individuals to reduce upfront capital expenditures on physical infrastructure by shifting to an operational expenditure model, where costs scale with usage. Cloud platforms also offer managed services and tools, such as artificial intelligence, data analytics, and machine learning, which might otherwise require significant in-house expertise and infrastructure investment.
While cloud computing can offer cost advantages through effective resource optimization, organizations often face challenges such as unused resources, inefficient configurations, and hidden costs without proper oversight and governance. Many cloud platforms provide cost management tools, such as AWS Cost Explorer and Azure Cost Management, and frameworks like FinOps have emerged to standardize financial operations in the cloud. Cloud computing also facilitates collaboration, remote work, and global service delivery by enabling secure access to data and applications from any location with an internet connection.
Cloud providers offer various redundancy options for core services, such as managed storage and managed databases, though redundancy configurations often vary by service tier. Advanced redundancy strategies, such as cross-region replication or failover systems, typically require explicit configuration and may incur additional costs or licensing fees.
Cloud environments operate under a shared responsibility model, where providers are typically responsible for infrastructure security, physical hardware, and software updates, while customers are accountable for data encryption, identity and access management (IAM), and application-level security. These responsibilities vary depending on the cloud service model—Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS)—with customers typically having more control and responsibility in IaaS environments and progressively less in PaaS and SaaS models, often trading control for convenience and managed services.
Factors Influencing Adoption and Suitability of Cloud Computing
The decision to adopt cloud computing or maintain on-premises infrastructure depends on factors such as scalability, cost structure, latency requirements, regulatory constraints, and infrastructure customization.
Organizations with variable or unpredictable workloads, limited capital for upfront investments, or a focus on rapid scalability benefit from cloud adoption. Startups, SaaS companies, and e-commerce platforms often prefer the pay-as-you-go operational expenditure (OpEx) model of cloud infrastructure. Additionally, companies prioritizing global accessibility, remote workforce enablement, disaster recovery, and leveraging advanced services such as AI/ML and analytics are well-suited for the cloud. In recent years, some cloud providers have started offering specialized services for high-performance computing and low-latency applications, addressing some use cases previously exclusive to on-premises setups.
On the other hand, organizations with strict regulatory requirements, highly predictable workloads, or reliance on deeply integrated legacy systems may find cloud infrastructure less suitable. Businesses in industries like defense, government, or those handling highly sensitive data often favor on-premises setups for greater control and data sovereignty. Additionally, companies with ultra-low latency requirements, such as high-frequency trading (HFT) firms, rely on custom hardware (e.g., FPGAs) and physical proximity to exchanges, which most cloud providers cannot fully replicate despite recent advancements. Similarly, tech giants like Google, Meta, and Amazon build their own data centers due to economies of scale, predictable workloads, and the ability to customize hardware and network infrastructure for optimal efficiency. However, these companies also use cloud services selectively for certain workloads and applications where it aligns with their operational needs.
In practice, many organizations are increasingly adopting hybrid cloud architectures, combining on-premises infrastructure with cloud services. This approach allows businesses to balance scalability, cost-effectiveness, and control, offering the benefits of both deployment models while mitigating their respective limitations.
Challenges and limitations
Main article: Cloud computing issuesOne of the main challenges of cloud computing, in comparison to more traditional on-premises computing, is data security and privacy. Cloud users entrust their sensitive data to third-party providers, who may not have adequate measures to protect it from unauthorized access, breaches, or leaks. Cloud users also face compliance risks if they have to adhere to certain regulations or standards regarding data protection, such as GDPR or HIPAA.
Another challenge of cloud computing is reduced visibility and control. Cloud users may not have full insight into how their cloud resources are managed, configured, or optimized by their providers. They may also have limited ability to customize or modify their cloud services according to their specific needs or preferences. Complete understanding of all technology may be impossible, especially given the scale, complexity, and deliberate opacity of contemporary systems; however, there is a need for understanding complex technologies and their interconnections to have power and agency within them. The metaphor of the cloud can be seen as problematic as cloud computing retains the aura of something noumenal and numinous; it is something experienced without precisely understanding what it is or how it works.
Additionally, cloud migration is a significant challenge. This process involves transferring data, applications, or workloads from one cloud environment to another, or from on-premises infrastructure to the cloud. Cloud migration can be complicated, time-consuming, and expensive, particularly when there are compatibility issues between different cloud platforms or architectures. If not carefully planned and executed, cloud migration can lead to downtime, reduced performance, or even data loss.
Cloud migration challenges
According to the 2024 State of the Cloud Report by Flexera, approximately 50% of respondents identified the following top challenges when migrating workloads to public clouds:
- "Understanding application dependencies"
- "Comparing on-premise and cloud costs"
- "Assessing technical feasibility."
Implementation challenges
Applications hosted in the cloud are susceptible to the fallacies of distributed computing, a series of misconceptions that can lead to significant issues in software development and deployment.
Cloud cost overruns
In a report by Gartner, a survey of 200 IT leaders revealed that 69% experienced budget overruns in their organizations' cloud expenditures during 2023. Conversely, 31% of IT leaders whose organizations stayed within budget attributed their success to accurate forecasting and budgeting, proactive monitoring of spending, and effective optimization.
The 2024 Flexera State of Cloud Report identifies the top cloud challenges as managing cloud spend, followed by security concerns and lack of expertise. Public cloud expenditures exceeded budgeted amounts by an average of 15%. The report also reveals that cost savings is the top cloud initiative for 60% of respondents. Furthermore, 65% measure cloud progress through cost savings, while 42% prioritize shorter time-to-market, indicating that cloud's promise of accelerated deployment is often overshadowed by cost concerns.
Service Level Agreements
Typically, cloud providers' Service Level Agreements (SLAs) do not encompass all forms of service interruptions. Exclusions typically include planned maintenance, downtime resulting from external factors such as network issues, human errors, like misconfigurations, natural disasters, force majeure events, or security breaches. Typically, customers bear the responsibility of monitoring SLA compliance and must file claims for any unmet SLAs within a designated timeframe. Customers should be aware of how deviations from SLAs are calculated, as these parameters may vary by service. These requirements can place a considerable burden on customers. Additionally, SLA percentages and conditions can differ across various services within the same provider, with some services lacking any SLA altogether. In cases of service interruptions due to hardware failures in the cloud provider, the company typically does not offer monetary compensation. Instead, eligible users may receive credits as outlined in the corresponding SLA.
Leaky abstractions
Cloud computing abstractions aim to simplify resource management, but leaky abstractions can expose underlying complexities. These variations in abstraction quality depend on the cloud vendor, service and architecture. Mitigating leaky abstractions requires users to understand the implementation details and limitations of the cloud services they utilize.
Service lock-in within the same vendor
Service lock-in within the same vendor occurs when a customer becomes dependent on specific services within a cloud vendor, making it challenging to switch to alternative services within the same vendor when their needs change.
Security and privacy

Cloud computing poses privacy concerns because the service provider can access the data that is in the cloud at any time. It could accidentally or deliberately alter or delete information. Many cloud providers can share information with third parties if necessary for purposes of law and order without a warrant. That is permitted in their privacy policies, which users must agree to before they start using cloud services. Solutions to privacy include policy and legislation as well as end-users' choices for how data is stored. Users can encrypt data that is processed or stored within the cloud to prevent unauthorized access. Identity management systems can also provide practical solutions to privacy concerns in cloud computing. These systems distinguish between authorized and unauthorized users and determine the amount of data that is accessible to each entity. The systems work by creating and describing identities, recording activities, and getting rid of unused identities.
According to the Cloud Security Alliance, the top three threats in the cloud are Insecure Interfaces and APIs, Data Loss & Leakage, and Hardware Failure—which accounted for 29%, 25% and 10% of all cloud security outages respectively. Together, these form shared technology vulnerabilities. In a cloud provider platform being shared by different users, there may be a possibility that information belonging to different customers resides on the same data server. Additionally, Eugene Schultz, chief technology officer at Emagined Security, said that hackers are spending substantial time and effort looking for ways to penetrate the cloud. "There are some real Achilles' heels in the cloud infrastructure that are making big holes for the bad guys to get into". Because data from hundreds or thousands of companies can be stored on large cloud servers, hackers can theoretically gain control of huge stores of information through a single attack—a process he called "hyperjacking". Some examples of this include the Dropbox security breach, and iCloud 2014 leak. Dropbox had been breached in October 2014, having over seven million of its users passwords stolen by hackers in an effort to get monetary value from it by Bitcoins (BTC). By having these passwords, they are able to read private data as well as have this data be indexed by search engines (making the information public).
There is the problem of legal ownership of the data (If a user stores some data in the cloud, can the cloud provider profit from it?). Many Terms of Service agreements are silent on the question of ownership. Physical control of the computer equipment (private cloud) is more secure than having the equipment off-site and under someone else's control (public cloud). This delivers great incentive to public cloud computing service providers to prioritize building and maintaining strong management of secure services. Some small businesses that do not have expertise in IT security could find that it is more secure for them to use a public cloud. There is the risk that end users do not understand the issues involved when signing on to a cloud service (persons sometimes do not read the many pages of the terms of service agreement, and just click "Accept" without reading). This is important now that cloud computing is common and required for some services to work, for example for an intelligent personal assistant (Apple's Siri or Google Assistant). Fundamentally, private cloud is seen as more secure with higher levels of control for the owner, however public cloud is seen to be more flexible and requires less time and money investment from the user.
The attacks that can be made on cloud computing systems include man-in-the middle attacks, phishing attacks, authentication attacks, and malware attacks. One of the largest threats is considered to be malware attacks, such as Trojan horses. Recent research conducted in 2022 has revealed that the Trojan horse injection method is a serious problem with harmful impacts on cloud computing systems.
Service models
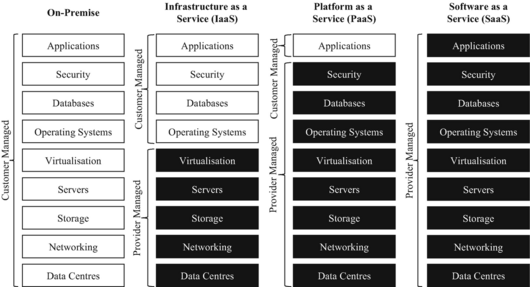

The National Institute of Standards and Technology recognized three cloud service models in 2011: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). The International Organization for Standardization (ISO) later identified additional models in 2023, including "Network as a Service", "Communications as a Service", "Compute as a Service", and "Data Storage as a Service".
Infrastructure as a service (IaaS)
Main article: Infrastructure as a serviceInfrastructure as a service (IaaS) refers to online services that provide high-level APIs used to abstract various low-level details of underlying network infrastructure like physical computing resources, location, data partitioning, scaling, security, backup, etc. A hypervisor runs the virtual machines as guests. Pools of hypervisors within the cloud operational system can support large numbers of virtual machines and the ability to scale services up and down according to customers' varying requirements. Linux containers run in isolated partitions of a single Linux kernel running directly on the physical hardware. Linux cgroups and namespaces are the underlying Linux kernel technologies used to isolate, secure and manage the containers. The use of containers offers higher performance than virtualization because there is no hypervisor overhead. IaaS clouds often offer additional resources such as a virtual-machine disk-image library, raw block storage, file or object storage, firewalls, load balancers, IP addresses, virtual local area networks (VLANs), and software bundles.
Further information: CloudBioLinuxThe NIST's definition of cloud computing describes IaaS as "where the consumer is able to deploy and run arbitrary software, which can include operating systems and applications. The consumer does not manage or control the underlying cloud infrastructure but has control over operating systems, storage, and deployed applications; and possibly limited control of select networking components (e.g., host firewalls)."
IaaS-cloud providers supply these resources on-demand from their large pools of equipment installed in data centers. For wide-area connectivity, customers can use either the Internet or carrier clouds (dedicated virtual private networks). To deploy their applications, cloud users install operating-system images and their application software on the cloud infrastructure. In this model, the cloud user patches and maintains the operating systems and the application software. Cloud providers typically bill IaaS services on a utility computing basis: cost reflects the number of resources allocated and consumed.
Platform as a service (PaaS)
Main article: Platform as a serviceThe NIST's definition of cloud computing defines Platform as a Service as:
The capability provided to the consumer is to deploy onto the cloud infrastructure consumer-created or acquired applications created using programming languages, libraries, services, and tools supported by the provider. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, or storage, but has control over the deployed applications and possibly configuration settings for the application-hosting environment.
PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a computing platform, typically including an operating system, programming-language execution environment, database, and the web server. Application developers develop and run their software on a cloud platform instead of directly buying and managing the underlying hardware and software layers. With some PaaS, the underlying computer and storage resources scale automatically to match application demand so that the cloud user does not have to allocate resources manually.
Some integration and data management providers also use specialized applications of PaaS as delivery models for data. Examples include iPaaS (Integration Platform as a Service) and dPaaS (Data Platform as a Service). iPaaS enables customers to develop, execute and govern integration flows. Under the iPaaS integration model, customers drive the development and deployment of integrations without installing or managing any hardware or middleware. dPaaS delivers integration—and data-management—products as a fully managed service. Under the dPaaS model, the PaaS provider, not the customer, manages the development and execution of programs by building data applications for the customer. dPaaS users access data through data-visualization tools.
Software as a service (SaaS)
Main article: Software as a serviceThe NIST's definition of cloud computing defines Software as a Service as:
The capability provided to the consumer is to use the provider's applications running on a cloud infrastructure. The applications are accessible from various client devices through either a thin client interface, such as a web browser (e.g., web-based email), or a program interface. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, storage, or even individual application capabilities, with the possible exception of limited user-specific application configuration settings.
In the software as a service (SaaS) model, users gain access to application software and databases. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee. In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability—which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand. Load balancers distribute the work over the set of virtual machines. This process is transparent to the cloud user, who sees only a single access-point. To accommodate a large number of cloud users, cloud applications can be multitenant, meaning that any machine may serve more than one cloud-user organization.
The pricing model for SaaS applications is typically a monthly or yearly flat fee per user, so prices become scalable and adjustable if users are added or removed at any point. It may also be free. Proponents claim that SaaS gives a business the potential to reduce IT operational costs by outsourcing hardware and software maintenance and support to the cloud provider. This enables the business to reallocate IT operations costs away from hardware/software spending and from personnel expenses, towards meeting other goals. In addition, with applications hosted centrally, updates can be released without the need for users to install new software. One drawback of SaaS comes with storing the users' data on the cloud provider's server. As a result, there could be unauthorized access to the data. Examples of applications offered as SaaS are games and productivity software like Google Docs and Office Online. SaaS applications may be integrated with cloud storage or File hosting services, which is the case with Google Docs being integrated with Google Drive, and Office Online being integrated with OneDrive.
Serverless computing
Main article: Serverless computingServerless computing allows customers to use various cloud capabilities without the need to provision, deploy, or manage hardware or software resources, apart from providing their application code or data. ISO/IEC 22123-2:2023 classifies serverless alongside Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) under the broader category of cloud service categories. Notably, while ISO refers to these classifications as cloud service categories, the National Institute of Standards and Technology (NIST) refers to them as service models.
Deployment models

"A cloud deployment model represents the way in which cloud computing can be organized based on the control and sharing of physical or virtual resources." Cloud deployment models define the fundamental patterns of interaction between cloud customers and cloud providers. They do not detail implementation specifics or the configuration of resources.
Private
Private cloud is cloud infrastructure operated solely for a single organization, whether managed internally or by a third party, and hosted either internally or externally. Undertaking a private cloud project requires significant engagement to virtualize the business environment, and requires the organization to reevaluate decisions about existing resources. It can improve business, but every step in the project raises security issues that must be addressed to prevent serious vulnerabilities. Self-run data centers are generally capital intensive. They have a significant physical footprint, requiring allocations of space, hardware, and environmental controls. These assets have to be refreshed periodically, resulting in additional capital expenditures. They have attracted criticism because users "still have to buy, build, and manage them" and thus do not benefit from less hands-on management, essentially " the economic model that makes cloud computing such an intriguing concept".
Public
For a comparison of cloud-computing software and providers, see Cloud-computing comparisonCloud services are considered "public" when they are delivered over the public Internet, and they may be offered as a paid subscription, or free of charge. Architecturally, there are few differences between public- and private-cloud services, but security concerns increase substantially when services (applications, storage, and other resources) are shared by multiple customers. Most public-cloud providers offer direct-connection services that allow customers to securely link their legacy data centers to their cloud-resident applications.
Several factors like the functionality of the solutions, cost, integrational and organizational aspects as well as safety & security are influencing the decision of enterprises and organizations to choose a public cloud or on-premises solution.
Hybrid
See also: Hybrid cloud storageHybrid cloud is a composition of a public cloud and a private environment, such as a private cloud or on-premises resources, that remain distinct entities but are bound together, offering the benefits of multiple deployment models. Hybrid cloud can also mean the ability to connect collocation, managed and/or dedicated services with cloud resources. Gartner defines a hybrid cloud service as a cloud computing service that is composed of some combination of private, public and community cloud services, from different service providers. A hybrid cloud service crosses isolation and provider boundaries so that it cannot be simply put in one category of private, public, or community cloud service. It allows one to extend either the capacity or the capability of a cloud service, by aggregation, integration or customization with another cloud service.
Varied use cases for hybrid cloud composition exist. For example, an organization may store sensitive client data in house on a private cloud application, but interconnect that application to a business intelligence application provided on a public cloud as a software service. This example of hybrid cloud extends the capabilities of the enterprise to deliver a specific business service through the addition of externally available public cloud services. Hybrid cloud adoption depends on a number of factors such as data security and compliance requirements, level of control needed over data, and the applications an organization uses.
Another example of hybrid cloud is one where IT organizations use public cloud computing resources to meet temporary capacity needs that can not be met by the private cloud. This capability enables hybrid clouds to employ cloud bursting for scaling across clouds. Cloud bursting is an application deployment model in which an application runs in a private cloud or data center and "bursts" to a public cloud when the demand for computing capacity increases. A primary advantage of cloud bursting and a hybrid cloud model is that an organization pays for extra compute resources only when they are needed. Cloud bursting enables data centers to create an in-house IT infrastructure that supports average workloads, and use cloud resources from public or private clouds, during spikes in processing demands.
Community
Community cloud shares infrastructure between several organizations from a specific community with common concerns (security, compliance, jurisdiction, etc.), whether it is managed internally or by a third-party, and hosted internally or externally, the costs are distributed among fewer users compared to a public cloud (but more than a private cloud). As a result, only a portion of the potential cost savings of cloud computing is achieved.
Multi cloud
Main article: MulticloudAccording to ISO/IEC 22123-1: "multi-cloud is a cloud deployment model in which a customer uses public cloud services provided by two or more cloud service providers". Poly cloud refers to the use of multiple public clouds for the purpose of leveraging specific services that each provider offers. It differs from Multi cloud in that it is not designed to increase flexibility or mitigate against failures but is rather used to allow an organization to achieve more than could be done with a single provider.
Market
According to International Data Corporation (IDC), global spending on cloud computing services has reached $706 billion and is expected to reach $1.3 trillion by 2025. Gartner estimated that global public cloud services end-user spending would reach $600 billion by 2023. According to a McKinsey & Company report, cloud cost-optimization levers and value-oriented business use cases foresee more than $1 trillion in run-rate EBITDA across Fortune 500 companies as up for grabs in 2030. In 2022, more than $1.3 trillion in enterprise IT spending was at stake from the shift to the cloud, growing to almost $1.8 trillion in 2025, according to Gartner.
The European Commission's 2012 Communication identified several issues which were impeding the development of the cloud computing market:
- fragmentation of the digital single market across the EU
- concerns about contracts including reservations about data access and ownership, data portability, and change control
- variations in standards applicable to cloud computing
The Communication set out a series of "digital agenda actions" which the Commission proposed to undertake in order to support the development of a fair and effective market for cloud computing services.
List of public clouds
- Adobe Creative Cloud
- Amazon Web Services
- Google Cloud
- IBM Cloud
- Microsoft Azure
- OpenStack
- Oracle Cloud
- Panorama9
Similar concepts
The goal of cloud computing is to allow users to take benefit from all of these technologies, without the need for deep knowledge about or expertise with each one of them. The cloud aims to cut costs and helps the users focus on their core business instead of being impeded by IT obstacles. The main enabling technology for cloud computing is virtualization. Virtualization software separates a physical computing device into one or more "virtual" devices, each of which can be easily used and managed to perform computing tasks. With operating system–level virtualization essentially creating a scalable system of multiple independent computing devices, idle computing resources can be allocated and used more efficiently. Virtualization provides the agility required to speed up IT operations and reduces cost by increasing infrastructure utilization. Autonomic computing automates the process through which the user can provision resources on-demand. By minimizing user involvement, automation speeds up the process, reduces labor costs and reduces the possibility of human errors.
Cloud computing uses concepts from utility computing to provide metrics for the services used. Cloud computing attempts to address QoS (quality of service) and reliability problems of other grid computing models.
Cloud computing shares characteristics with:
- Client–server model – Client–server computing refers broadly to any distributed application that distinguishes between service providers (servers) and service requestors (clients).
- Computer bureau – A service bureau providing computer services, particularly from the 1960s to 1980s.
- Grid computing – A form of distributed and parallel computing, whereby a 'super and virtual computer' is composed of a cluster of networked, loosely coupled computers acting in concert to perform very large tasks.
- Fog computing – Distributed computing paradigm that provides data, compute, storage and application services closer to the client or near-user edge devices, such as network routers. Furthermore, fog computing handles data at the network level, on smart devices and on the end-user client-side (e.g. mobile devices), instead of sending data to a remote location for processing.
- Utility computing – The "packaging of computing resources, such as computation and storage, as a metered service similar to a traditional public utility, such as electricity."
- Peer-to-peer – A distributed architecture without the need for central coordination. Participants are both suppliers and consumers of resources (in contrast to the traditional client-server model).
- Cloud sandbox – A live, isolated computer environment in which a program, code or file can run without affecting the application in which it runs.
See also
- As a service
- Block-level storage
- Browser-based computing
- Category:Cloud computing providers
- Category:Cloud platforms
- Cloud computing architecture
- Cloud broker
- Cloud collaboration
- Cloud-computing comparison
- Cloud computing security
- Cloud engineering
- Cloud gaming
- Cloud management
- Cloud-native computing
- Cloud research
- Cloud robotics
- Cloud storage
- Cloud-to-cloud integration
- Cloudlet
- Computer cluster
- Cooperative storage cloud
- Decentralized computing
- Desktop virtualization
- Dew computing
- Directory
- Distributed data store
- Distributed database
- Distributed computing
- Distributed networking
- e-Science
- Edge computing
- Edge device
- File system
- Fog computing
- Fog robotics
- Green computing (environmentally sustainable computing)
- Grid computing
- In-memory database
- In-memory processing
- Internet of things
- IoT security device
- Knowledge as a service
- Microservices
- Mobile cloud computing
- Multi-access edge computing
- Multisite cloud
- Peer-to-peer
- Personal cloud
- Private cloud computing infrastructure
- Robot as a service
- Service-oriented architecture
- Time-sharing
- Ubiquitous computing
- Virtual private cloud
Notes
References
- "ISO/IEC 22123-1:2023(E) - Information technology - Cloud computing - Part 1: Vocabulary". International Organization for Standardization. 2023.
- ^ Mell, Peter; Timothy Grance (September 2011). The NIST Definition of Cloud Computing (Technical report). National Institute of Standards and Technology: U.S. Department of Commerce. doi:10.6028/NIST.SP.800-145. Special publication 800-145.
- ^ "ISO/IEC 22123-2:2023(E) - Information technology — Cloud computing — Part 2: Concepts". International Organization for Standardization. September 2023.
- James E. White (March 1971). Network Specifications for Remote Job Entry and Remote Job Output Retrieval at UCSB. Network Working Group. doi:10.17487/RFC0105. RFC 105. Status Unknown. Updated by RFC 217
- Levy, Steven (April 1994). "Bill and Andy's Excellent Adventure II". Wired. Archived from the original on 2015-10-02.
- Mosco, Vincent (2015). To the Cloud: Big Data in a Turbulent World. Taylor & Francis. p. 15. ISBN 9781317250388.
- "Announcing Amazon Elastic Compute Cloud (Amazon EC2) – beta". 24 August 2006. Archived from the original on 13 August 2014. Retrieved 31 May 2014.
- Qian, Ling; Lou, Zhigou; Du, Yujian; Gou, Leitao. "Cloud Computing: An Overview". Retrieved 19 April 2021.
- "Windows Azure General Availability". The Official Microsoft Blog. Microsoft. 2010-02-01. Archived from the original on 2014-05-11. Retrieved 2015-05-03.
- "Announcing General Availability of AWS Outposts". Amazon Web Services, Inc. Archived from the original on 2021-01-21. Retrieved 2021-02-04.
- ^ Cloud Computing: Concepts, Technology & Architecture. ISBN 978-0133387520.
- ^ Cloud Computing, revised and updated edition. ISBN 978-0262546478.
- ^ Cloud Computing. ISBN 978-1284233971.
- ^ Cloud Computing For Dummies. ISBN 978-0470484708.
- ^ Hybrid Cloud for Architects: Build robust hybrid cloud solutions using AWS and OpenStack. ISBN 9781788623513.
- ^ Security Architecture for Hybrid Cloud: A Practical Method for Designing Security Using Zero Trust Principles. ISBN 9781098157777.
- ^ Architecting the Cloud: Design Decisions for Cloud Computing Service Models (SaaS, PaaS, and IaaS). ISBN 978-1118617618.
- ^ Marko, Kurt; Bigelow, Stephen J. (10 Nov 2022). "The pros and cons of cloud computing explained". TechTarget.
- Bratton, Benjamin H. (2015). The stack: on software and sovereignty. Software studies. Cambridge, Mass. London: MIT press. ISBN 978-0-262-02957-5.
- Bridle, James (2019). New dark age: technology and the end of the future. Verso.
- Shurma, Ramesh (8 Mar 2023). "The Hidden Costs Of Cloud Migration". Forbes.
- ^ "2024 State of the Cloud Report". Flexera's State of the Cloud Report.
- Fundamentals of Software Architecture: An Engineering Approach. O'Reilly Media. 2020. ISBN 978-1492043454.
- "2024 Cloud Spending: IT Balances Costs with GenAI Innovation". Gartner Peer Community. Retrieved Nov 16, 2024.
- Cloud Security and Privacy An Enterprise Perspective on Risks and Compliance. O'Reilly Media. 4 September 2009. ISBN 9781449379513.
- Requirements Engineering for Service and Cloud Computing. Springer International Publishing. 10 April 2017. ISBN 9783319513102.
- Srinivasan (14 May 2014). Cloud Computing Basics. Springer. ISBN 9781461476993.
- Murugesan, San (August 2016). Encyclopedia of Cloud Computing. John Wiley & Sons. ISBN 9781118821978.
- Cloud Native Infrastructure: Patterns for Scalable Infrastructure and Applications in a Dynamic Environment. O'Reilly Media. 25 October 2017. ISBN 9781491984253.
- Hausenblas, Michael (26 December 2023). Cloud Observability in Action. Simon and Schuster. ISBN 9781633439597.
- Jr, Cloves Carneiro; Schmelmer, Tim (10 December 2016). Microservices From Day One: Build robust and scalable software from the start. Apress. ISBN 9781484219379.
- Jennings, Roger (29 December 2010). Cloud Computing with the Windows Azure Platform. John Wiley & Sons. ISBN 9781118058756.
- Cloud and Virtual Data Storage Networking. ISBN 9781466508446.
- ^ Ryan, Mark D. (January 2011). "Cloud Computing Privacy Concerns on Our Doorstep". cacm.acm.org. Archived from the original on 2021-12-28. Retrieved 2021-05-21.
- Indu, I.; Anand, P.M. Rubesh; Bhaskar, Vidhyacharan (August 1, 2018). "Identity and access management in cloud environment: Mechanisms and challenges". Engineering Science and Technology. 21 (4): 574–588. doi:10.1016/j.jestch.2018.05.010.
- ^ "Google Drive, Dropbox, Box and iCloud Reach the Top 5 Cloud Storage Security Breaches List". psg.hitachi-solutions.com. Archived from the original on 2015-11-23. Retrieved 2015-11-22.
- Maltais, Michelle (26 April 2012). "Who owns your stuff in the cloud?". Los Angeles Times. Archived from the original on 2013-01-20. Retrieved 2012-12-14.
- "Security of virtualization, cloud computing divides IT and security pros". Network World. 2010-02-22. Archived from the original on 2024-04-26. Retrieved 2010-08-22.
- "The Bumpy Road to Private Clouds". 2010-12-20. Archived from the original on 2014-10-15. Retrieved 8 October 2014.
- Kanaker, Hasan; Karim, Nader Abdel; Awwad, Samer A. B.; Ismail, Nurul H. A.; Zraqou, Jamal; Ali, Abdulla M. F. Al (2022-12-20). "Trojan Horse Infection Detection in Cloud Based Environment Using Machine Learning". International Journal of Interactive Mobile Technologies. 16 (24): 81–106. doi:10.3991/ijim.v16i24.35763. ISSN 1865-7923. S2CID 254960874.
- Amies, Alex; Sluiman, Harm; Tong, Qiang Guo; Liu, Guo Ning (July 2012). "Infrastructure as a Service Cloud Concepts". Developing and Hosting Applications on the Cloud. IBM Press. ISBN 978-0-13-306684-5. Archived from the original on 2012-09-15. Retrieved 2012-07-19.
- Nelson, Michael R. (2009). "The Cloud, the Crowd, and Public Policy". Issues in Science and Technology. 25 (4): 71–76. JSTOR 43314918. Archived from the original on 2022-09-10. Retrieved 2022-09-10.
- Boniface, M.; et al. (2010). Platform-as-a-Service Architecture for Real-Time Quality of Service Management in Clouds. 5th International Conference on Internet and Web Applications and Services (ICIW). Barcelona, Spain: IEEE. pp. 155–160. doi:10.1109/ICIW.2010.91.
- "Integration Platform as a Service (iPaaS)". Gartner IT Glossary. Gartner. Archived from the original on 2015-07-29. Retrieved 2015-07-20.
- Gartner; Massimo Pezzini; Paolo Malinverno; Eric Thoo. "Gartner Reference Model for Integration PaaS". Archived from the original on 1 July 2013. Retrieved 16 January 2013.
- Loraine Lawson (3 April 2015). "IT Business Edge". Archived from the original on 7 July 2015. Retrieved 6 July 2015.
- Enterprise CIO Forum; Gabriel Lowy. "The Value of Data Platform-as-a-Service (dPaaS)". Archived from the original on 19 April 2015. Retrieved 6 July 2015.
- "Definition of: SaaS". PC Magazine Encyclopedia. Ziff Davis. Archived from the original on 14 July 2014. Retrieved 14 May 2014.
- Hamdaqa, Mohammad. A Reference Model for Developing Cloud Applications (PDF). Archived (PDF) from the original on 2012-10-05. Retrieved 2012-05-23.
- Chou, Timothy. Introduction to Cloud Computing: Business & Technology. Archived from the original on 2016-05-05. Retrieved 2017-09-09.
- "HVD: the cloud's silver lining" (PDF). Intrinsic Technology. Archived from the original (PDF) on 2 October 2012. Retrieved 30 August 2012.
- Sun, Yunchuan; Zhang, Junsheng; Xiong, Yongping; Zhu, Guangyu (2014-07-01). "Data Security and Privacy in Cloud Computing". International Journal of Distributed Sensor Networks. 10 (7): 190903. doi:10.1155/2014/190903. ISSN 1550-1477. S2CID 13213544.
- "Use OneDrive with Office". Microsoft Support. Archived from the original on 2022-10-15. Retrieved 2022-10-15.
- "Self-Run Private Cloud Computing Solution – GovConnection". govconnection.com. 2014. Archived from the original on April 6, 2014. Retrieved April 15, 2014.
- "Private Clouds Take Shape – Services – Business services – Informationweek". 2012-09-09. Archived from the original on 2012-09-09.
- Haff, Gordon (2009-01-27). "Just don't call them private clouds". CNET News. Archived from the original on 2014-12-27. Retrieved 2010-08-22.
- "There's No Such Thing As A Private Cloud – Cloud-computing -". 2013-01-26. Archived from the original on 2013-01-26.
- Rouse, Margaret. "What is public cloud?". Definition from Whatis.com. Archived from the original on 16 October 2014. Retrieved 12 October 2014.
- "Defining 'Cloud Services' and "Cloud Computing"". IDC. 2008-09-23. Archived from the original on 2010-07-22. Retrieved 2010-08-22.
- "FastConnect | Oracle Cloud Infrastructure". cloud.oracle.com. Archived from the original on 2017-11-15. Retrieved 2017-11-15.
- Schmidt, Rainer; Möhring, Michael; Keller, Barbara (2017). "Customer Relationship Management in a Public Cloud environment - Key influencing factors for European enterprises". HICSS. Proceedings of the 50th Hawaii International Conference on System Sciences (2017). doi:10.24251/HICSS.2017.513. hdl:10125/41673. ISBN 9780998133102.
- "What is hybrid cloud? - Definition from WhatIs.com". SearchCloudComputing. Archived from the original on 2019-07-16. Retrieved 2019-08-10.
- Butler, Brandon (2017-10-17). "What is hybrid cloud computing? The benefits of mixing private and public cloud services". Network World. Archived from the original on 2019-08-11. Retrieved 2019-08-11.
- "Mind the Gap: Here Comes Hybrid Cloud – Thomas Bittman". Thomas Bittman. 24 September 2012. Archived from the original on 17 April 2015. Retrieved 22 April 2015.
- "Business Intelligence Takes to Cloud for Small Businesses". CIO.com. 2014-06-04. Archived from the original on 2014-06-07. Retrieved 2014-06-04.
- Désiré Athow (24 August 2014). "Hybrid cloud: is it right for your business?". TechRadar. Archived from the original on 7 July 2017. Retrieved 22 April 2015.
- Metzler, Jim; Taylor, Steve. (2010-08-23) "Cloud computing: Reality vs. fiction" Archived 2013-06-19 at the Wayback Machine, Network World.
- Rouse, Margaret. "Definition: Cloudbursting" Archived 2013-03-19 at the Wayback Machine, May 2011. SearchCloudComputing.com.
- "How Cloudbursting "Rightsizes" the Data Center". 2012-06-22. Archived from the original on 2016-10-19. Retrieved 2016-10-19.
- "ISO/IEC 22123-1:2023(E) - Information technology — Cloud computing — Part 1: Vocabulary". International Organization for Standardization: 2.
- Gall, Richard (2018-05-16). "Polycloud: a better alternative to cloud agnosticism". Packt Hub. Archived from the original on 2019-11-11. Retrieved 2019-11-11.
- "IDC Forecasts Worldwide "Whole Cloud" Spending to Reach $1.3 Trillion by 2025". Idc.com. 2021-09-14. Archived from the original on 2022-07-29. Retrieved 2022-07-30.
- "Gartner Forecasts Worldwide Public Cloud End-User Spending to Reach Nearly $500 Billion in 2022". Archived from the original on 2022-07-25. Retrieved 2022-07-25.
- "Cloud's trillion-dollar prize is up for grabs". McKinsey. Archived from the original on 2022-07-25. Retrieved 2022-07-30.
- "Gartner Says More Than Half of Enterprise IT Spending in Key Market Segments Will Shift to the Cloud by 2025". Archived from the original on 2022-07-25. Retrieved 2022-07-25.
- ^ European Commission, Unleashing the Potential of Cloud Computing in Europe, COM(2012) 529 final, page 3, published 27 September 2012, accessed 26 April 2024
- ^ HAMDAQA, Mohammad (2012). Cloud Computing Uncovered: A Research Landscape (PDF). Elsevier Press. pp. 41–85. ISBN 978-0-12-396535-6. Archived (PDF) from the original on 2013-06-19. Retrieved 2013-03-19.
- "Distributed Application Architecture" (PDF). Sun Microsystem. Archived (PDF) from the original on 2011-04-06. Retrieved 2009-06-16.
- Vaquero, Luis M.; Rodero-Merino, Luis; Caceres, Juan; Lindner, Maik (December 2008). "A break in the clouds: Towards a cloud definition". ACM SIGCOMM Computer Communication Review. 39 (1): 50–55. doi:10.1145/1496091.1496100. S2CID 207171174.
- Danielson, Krissi (2008-03-26). "Distinguishing Cloud Computing from Utility Computing". Ebizq.net. Archived from the original on 2017-11-10. Retrieved 2010-08-22.
Further reading
- Millard, Christopher (2013). Cloud Computing Law. Oxford University Press. ISBN 978-0-19-967168-7.
- Weisser, Alexander (2020). International Taxation of Cloud Computing. Editions Juridiques Libres, ISBN 978-2-88954-030-3.
- Singh, Jatinder; Powles, Julia; Pasquier, Thomas; Bacon, Jean (July 2015). "Data Flow Management and Compliance in Cloud Computing". IEEE Cloud Computing. 2 (4): 24–32. doi:10.1109/MCC.2015.69. S2CID 9812531.
- Armbrust, Michael; Stoica, Ion; Zaharia, Matei; Fox, Armando; Griffith, Rean; Joseph, Anthony D.; Katz, Randy; Konwinski, Andy; Lee, Gunho; Patterson, David; Rabkin, Ariel (1 April 2010). "A view of cloud computing". Communications of the ACM. 53 (4): 50. doi:10.1145/1721654.1721672. S2CID 1673644.
- Hu, Tung-Hui (2015). A Prehistory of the Cloud. MIT Press. ISBN 978-0-262-02951-3.
- Mell, P. (2011, September). The NIST Definition of Cloud Computing. Retrieved November 1, 2015, from National Institute of Standards and Technology website
![]() Media related to Cloud computing at Wikimedia Commons
Media related to Cloud computing at Wikimedia Commons
| Parallel computing | |
|---|---|
| General | |
| Levels | |
| Multithreading | |
| Theory | |
| Elements | |
| Coordination | |
| Programming | |
| Hardware | |
| APIs | |
| Problems | |